ЫуЗЈЗжЮі
БОЮФеТжаЫљгаФкШнНіЙЉбЇЯАНЛСїЪЙгУЃЌВЛгУгкЦфЫћШЮКЮФПЕФЃЌбЯНћгУгкЩЬвЕгУЭОКЭЗЧЗЈгУЭОЃЌЗёдђгЩДЫВњЩњЕФвЛЧаКѓЙћОљгызїепЮоЙиЃЛ
БОЮФеТЮДОаэПЩНћжЙзЊдиЃЌНћжЙШЮКЮаоИФКѓЖўДЮДЋВЅЃЌЩУздЪЙгУБОЮФЩцМАЕФММЪѕЖјЕМжТЕФШЮКЮвтЭтЃЌзїепОљВЛИКд№ЃЛ
1. ИХЪі
АќУћЃКcom.hpbr.bosszhipin
АцБОЃК13.141
- ЮвУЧЕФФПБъЪЧЫбЫїЃЌашвЊЬсЧАЕЧТМЃЛЫуЗЈећЬхФбЖШЫужаЕШЃЛ
- змЬхЩцМАmd5ЁЂrc4ЁЂbase64ЁЂLZбЙЫѕетМИИіЖЋЮїЃЌашвЊЬсЧАСЫНтвЛЯТетаЉЫуЗЈЃЛ
2. зЅАќ&ЖЈЮЛ
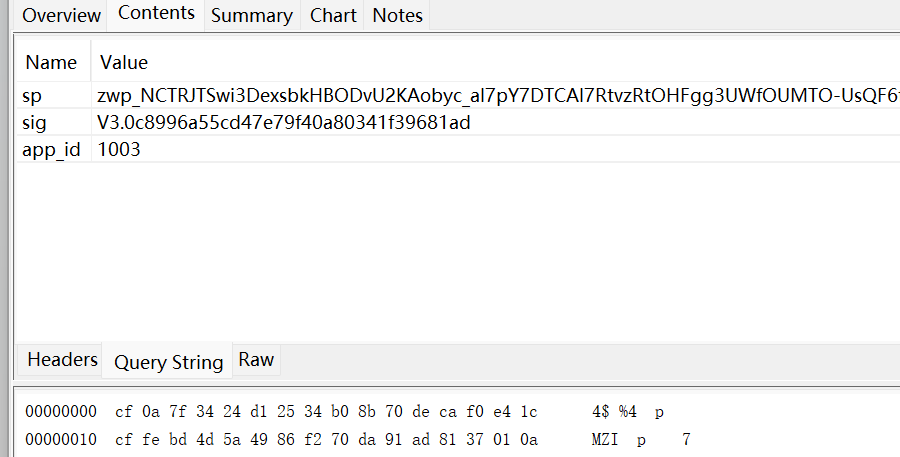
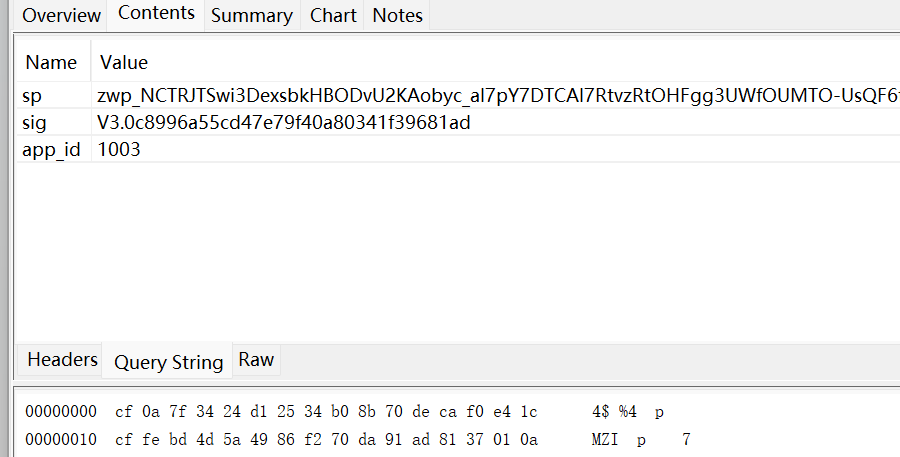
- ЪзЯШНјаазЅАќЃЌШЗЖЈФПБъВЮЪ§ЃЛЫбЫїжЎКѓев/api/batch/batchRunV2етИіНгПкЃЌжївЊФПБъЪЧspЁЂsigЁЂЛЙгаЗЕЛижЕПДЦ№РДЪЧМгУмЕФЃЌНгЯТРДОЭж№ИіЗжЮіЃЛ
- ЙРМЦЫќУЧВЛвЛЖЈдкЭЌвЛИіЮЛжУЃЌЯШПДПДАЩЃЌЖЈЮЛВЩгУЪВУДЗНЪНЖМПЩвдЃЌФмЖЈЮЛЕНЕФЗНЗЈЖМЪЧКУЗНЗЈЃЛ
- жБНгЫбЫїЖЈЮЛПДПДЃЌгаУЛгаБШНЯЯдблЕФЮЛжУЃЛ
- зюКѓвЛИіЯдШЛЪЧвЊКЯРэвЛЕуЕФЃЌНјШЅПДПДЃЛ
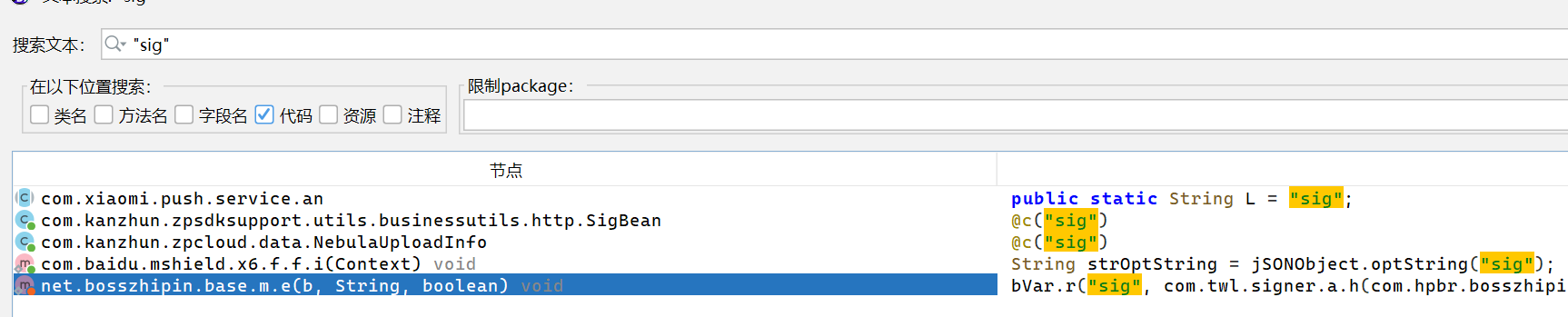
- sigКЭspЖМдкЃЌгаПЩФмЪЧетРяЃЌМЬајИњвЛЯТОЭПЩвдЗЂЯТЫќУЧЕФnativeКЏЪ§ЃЌЮвВЛЗХЭМСЫЃЌАбЖдгІЕФНсЙћаДЯТРДАЩЃЛ
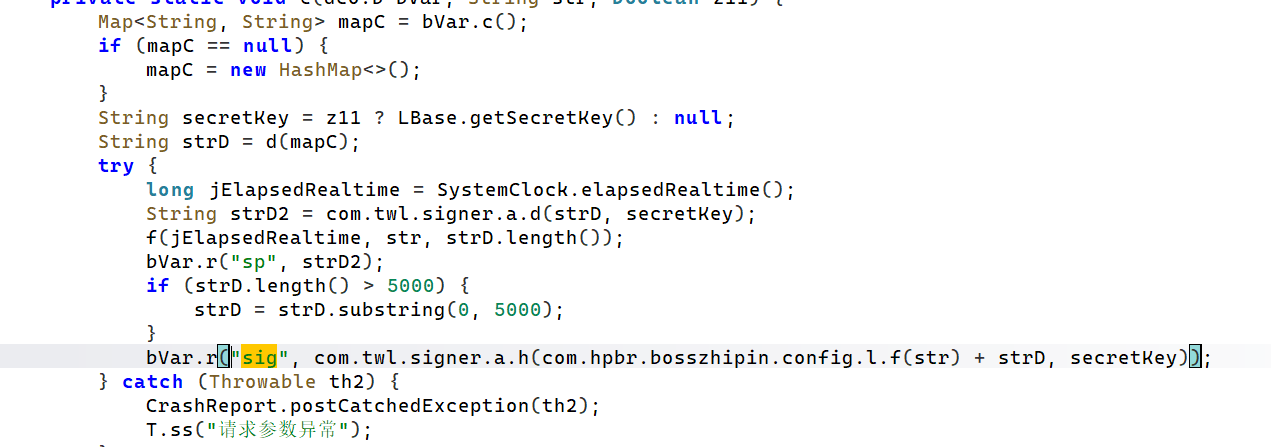
sigЃКprivate static native byte[] nativeSignature(byte[] bArr, String str);
spЃК private static native String nativeEncodeRequest(byte[] bArr, String str);
- ЖдгІЕФsoгІИУЪЧlibyzwg.soЃЛ
private static final String LIB_NAME = "yzwg";
function showByteArray(byteArray, name) {
if (byteArray == null) return;
var result = Java.use('java.lang.String').$new(Java.array('byte', byteArray)).toString();
console.log(name + ": " + result);
}
function hook_sig() {
Java.perform(function () {
let com_twl_signer_YZWG = Java.use("com.twl.signer.YZWG");
com_twl_signer_YZWG["nativeSignature"].implementation = function (bArr, str) {
console.log(`[->] chook_sig ->str= ${str}`);
showByteArray(bArr, "hook_sig bArr");
var retval = this["nativeSignature"](bArr, str);
showByteArray(retval, "hook_sig ЗЕЛижЕ")
return retval;
};
});
}
function hook_sp() {
Java.perform(function () {
let com_twl_signer_YZWG = Java.use("com.twl.signer.YZWG");
com_twl_signer_YZWG["nativeEncodeRequest"].implementation = function (bArr, str) {
console.log(`[->] hook_sp ->str= ${str}`);
showByteArray(bArr, "hook_sp bArr");
var retval = this["nativeEncodeRequest"](bArr, str);
console.log(`[<-] hook_sp retval= ${retval}`);
return retval;
};
});
}
hook_sig();
hook_sp();
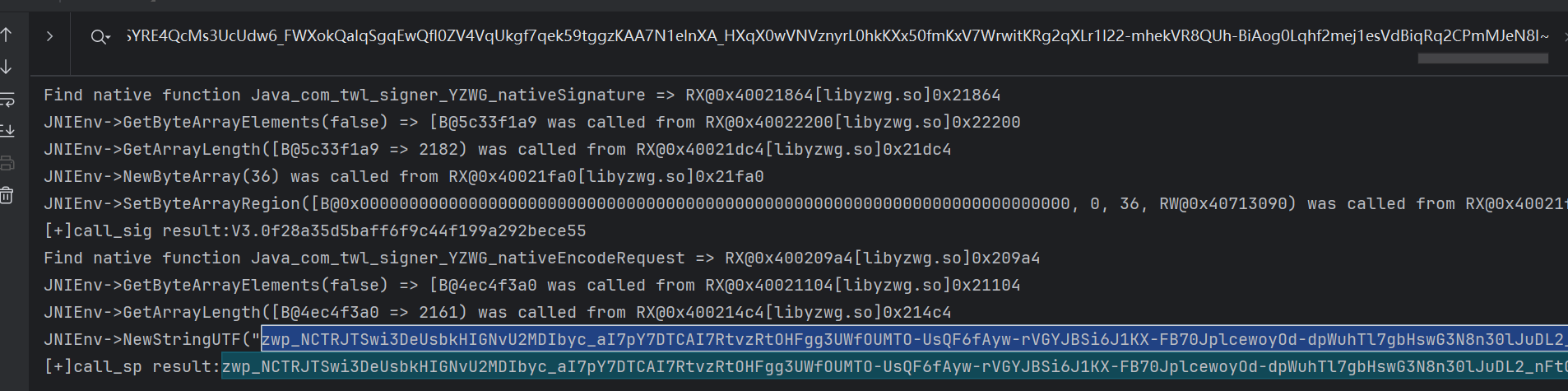
- hookНсЙћШчЯТЃЌЮвжЛеЙЪОКЭФПБъНгПкЖдгІЕФВПЗжЃЌвђЮЊНгПкДЅЗЂПЩФмБШНЯЖрЃЛ
[->] hook_sp ->str= null
hook_sp bArr: batch_method_feed=%5B%22method%3Dzpgeek.app.geek.search.cardlist%26encryptExpectId%3D4617621d9b2479b31nZ82tu0FFRSwA%257E%257E%26expectId%3D1261694622%26filterParams%3D%257B%2522cityCode%2522%253A%2522101010100%2522%252C%2522chattedJob%2522%253A0%252C%2522switchCity%2522%253A0%252C%2522labelFilter%2522%253A%257B%2522tags%2522%253A%255B%257B%2522code%2522%253A%2522-1%2522%252C%2522tag%2522%253A%2522%25E4%25B8%258D%25E9%2599%2590%2522%257D%255D%252C%2522type%2522%253A2%257D%257D%26isFromJd%3D0%26isSupplySearch%3Dfalse%26jids%3D%26maskComType%3D0%26naturalLanguageParam%3D%26noCorrect%3D0%26page%3D1%26prefix%3Dh%26pushId%3D%26pushType%3D%26query%3Dpython%26queryId%3D%26queryTitle%3D%25E6%2590%259C%25E7%25B4%25A2%25E5%258F%2591%25E7%258E%25B0%26searchType%3D3%26sort%3D-1%26source%3D1%26sugAbKey%3DM69-GroupA%26sugSessionId%3D1VpO529c1Ho%26userIntent%3D%22%2C+%22method%3Dzpgeek.app.search.listad.query%26encryptExpectId%3D4617621d9b2479b31nZ82tu0FFRSwA%257E%257E%26filterParams%3D%257B%2522cityCode%2522%253A%2522101010100%2522%252C%2522chattedJob%2522%253A0%252C%2522switchCity%2522%253A0%252C%2522labelFilter%2522%253A%257B%2522tags%2522%253A%255B%257B%2522code%2522%253A%2522-1%2522%252C%2522tag%2522%253A%2522%25E4%25B8%258D%25E9%2599%2590%2522%257D%255D%252C%2522type%2522%253A2%257D%257D%26page%3D1%26query%3Dpython%26sort%3D-1%22%5D&client_info=%7B%22version%22%3A%2212%22%2C%22os%22%3A%22Android%22%2C%22start_time%22%3A%221771739823352%22%2C%22resume_time%22%3A%221771739823352%22%2C%22channel%22%3A%2228%22%2C%22model%22%3A%22google%7C%7CPixel+6%22%2C%22dzt%22%3A0%2C%22loc_per%22%3A0%2C%22uniqid%22%3A%223880525a-bdb9-41fb-b8bc-b38d1addd229%22%2C%22oaid%22%3A%2200000000-0000-0000-0000-000000000000%22%2C%22oaid_honor%22%3A%2200000000-0000-0000-0000-000000000000%22%2C%22did%22%3A%22DUYlEEPTkR_1kujGVuif0etPK8a41fRRHAa0RFVZbEVFUFRrUl8xa3VqR1Z1aWYwZXRQSzhhNDFmUlJIQWEwc2h1%22%2C%22tinker_id%22%3A%22Prod-arm64-v8a-release-13.141.1314110_0812-10-06-09%22%2C%22is_bg_req%22%3A0%2C%22network%22%3A%22wifi%22%2C%22operator%22%3A%22UNKNOWN%22%2C%22abi%22%3A1%7D&curidentity=0&req_time=1771741084302&uniqid=3880525a-bdb9-41fb-b8bc-b38d1addd229&v=13.141
[<-] hook_sp retval= zwp_NCTRJTSwi3DeUsbkHIGNvU2MDIbyc_aI7pY7DTCAI7RtvzRtOHFgg3UWfOUMTO-UsQF6fAyw-rVGYJBSi6J1KX-FB70JplcewoyOd-dpWuhTl7gbHswG3N8n30lJuDL2_nFt0ONQG0-n42W9F8pD_iIs5mq-AKEi0RN8II4pDgJnH9pbEYKs0O0saFB8dqc6YRZJEJ0Iie7ZpgbwE2wwiQ_MU0Ko9XgrB6fBA_1dNFmp8z_--LNoBZBVyly3CrZasgjpOc5CqKwRiUrLgeb7BHBrymEAHlZDe_BQ8P1lQpGLHh-drdx6NqVHe86G_duGsfA0DoPuKyRaOSH75-PTb9Yub10pIs6LahfPutgSjC2BC09B1CSPjQPp8V2iQL20_x_unCd8sM5VGCTCr3fp9uIE18Rr7h2AMpAfS2xulAGlUjQhDFlyLkNvAWwbXzxVw8ax66GA9lv2bMdJVgs1HyvLF0rTX_ogaeu1FtgtPcGwzQcZ6ePWCAz2ciJdGH_u06080i88ensJkyDQDsnuuq-II60b4YmmKcHvUajXdbx0cDa1ycsUdnY-MDgKcLCbmgrDR5yX2dwcK7j8CzlC0SIQciE6Uc0SmPvpotX-eMKVGNlvblAg-XhXapAGzh7FwgfkDhGobrDNJ7lrCGu7IsKm-LAmuBPJUwV5QX0rWlkMM2xbo4UF1CskcpwwdPGEmg5eNxblPz3twdT_J6UqTMf63ORXTdROYuRT5D12saAMLm6gcjeaSk06KWura_DeVO_10mNKdk7yPf1rtwWuiG2WVwGKZLm7Oab_6NREKqkHMiXBc0d0r7hIWoC0Hi1aAB-h1boc91JBaZYLMN1tq3QWhDr_E0MrsjIHAO_jLhC56IcCQIYg44lmg3nvwrcbpqr6LzM6484_mTRummQWwOr5QFbqFtucP_elAVo5oNqbL_UrpbNjpcd_IdRn1wN4ak9HgBKWyXZvz1t-DNAGzA-EY-P_oP5etPcmoeO5C4Mt8eU-w_HO4aJljV0CQU_KnxyKB9Jfo_7o3E61W38LSlX6vxfaMQtmVDNjzERTXoMK73Q0KnWdd9RQEwn2bL1f9ruh2ngZvUG4PRaFp5w9dMq2-u-VU-0yjIJN81kbWcvHDoEVtT5MdubBYy3uNhetDoKY1NiiOFK7RWsDSB_K_a1ULaxaW2mun3Q4Qt8bkz4QyNwTF146dPhJxzrDQpx0ExNMvmBQRi7I9H-DY-ZJBLSIBn8tOSeb-2nWWN2cP_dl2Li9vk9jk5megfnb8LplyyA6WfD2MXhjYkVvUTgJ403oy0bYGYE7An3wOGOkmmK2Ip84EYPnKfcuMsihH-QUfUPzDGX-QWFzdj9X8GoEwevatOO0itUY7aMfLcW9icX0pziGDXIGv1rCo5xZSteXjc7besqHQpAxSkVKeqa2KQt33XmCjeJgE-Oh5X_ENG4bH7q5I9HLaLPBox7hSSUbq9NHay29dAZCPwujW9JnLsrm8BdACCpjO62Zl7IkKgoQ3ZgmQIkk1PYqUWSoOYMXQHCxL9SYRE4QcMs3UcUdw6_FWXokQalqSgqEwQfI0ZV4VqUkgf7qek59tggzKAA7N1eInXA_HXqX0wVNVznyrL0hkKXx50fmKxV7WrwitKRg2qXLr1I22-mhekVR8QUh-BiAog0Lqhf2mej1esVdBiqRq2CPmMJeN8I~
[->] chook_sig ->str= null
hook_sig bArr: /api/batch/batchRunV2batch_method_feed=%5B%22method%3Dzpgeek.app.geek.search.cardlist%26encryptExpectId%3D4617621d9b2479b31nZ82tu0FFRSwA%257E%257E%26expectId%3D1261694622%26filterParams%3D%257B%2522cityCode%2522%253A%2522101010100%2522%252C%2522chattedJob%2522%253A0%252C%2522switchCity%2522%253A0%252C%2522labelFilter%2522%253A%257B%2522tags%2522%253A%255B%257B%2522code%2522%253A%2522-1%2522%252C%2522tag%2522%253A%2522%25E4%25B8%258D%25E9%2599%2590%2522%257D%255D%252C%2522type%2522%253A2%257D%257D%26isFromJd%3D0%26isSupplySearch%3Dfalse%26jids%3D%26maskComType%3D0%26naturalLanguageParam%3D%26noCorrect%3D0%26page%3D1%26prefix%3Dh%26pushId%3D%26pushType%3D%26query%3Dpython%26queryId%3D%26queryTitle%3D%25E6%2590%259C%25E7%25B4%25A2%25E5%258F%2591%25E7%258E%25B0%26searchType%3D3%26sort%3D-1%26source%3D1%26sugAbKey%3DM69-GroupA%26sugSessionId%3D1VpO529c1Ho%26userIntent%3D%22%2C+%22method%3Dzpgeek.app.search.listad.query%26encryptExpectId%3D4617621d9b2479b31nZ82tu0FFRSwA%257E%257E%26filterParams%3D%257B%2522cityCode%2522%253A%2522101010100%2522%252C%2522chattedJob%2522%253A0%252C%2522switchCity%2522%253A0%252C%2522labelFilter%2522%253A%257B%2522tags%2522%253A%255B%257B%2522code%2522%253A%2522-1%2522%252C%2522tag%2522%253A%2522%25E4%25B8%258D%25E9%2599%2590%2522%257D%255D%252C%2522type%2522%253A2%257D%257D%26page%3D1%26query%3Dpython%26sort%3D-1%22%5D&client_info=%7B%22version%22%3A%2212%22%2C%22os%22%3A%22Android%22%2C%22start_time%22%3A%221771739823352%22%2C%22resume_time%22%3A%221771739823352%22%2C%22channel%22%3A%2228%22%2C%22model%22%3A%22google%7C%7CPixel+6%22%2C%22dzt%22%3A0%2C%22loc_per%22%3A0%2C%22uniqid%22%3A%223880525a-bdb9-41fb-b8bc-b38d1addd229%22%2C%22oaid%22%3A%2200000000-0000-0000-0000-000000000000%22%2C%22oaid_honor%22%3A%2200000000-0000-0000-0000-000000000000%22%2C%22did%22%3A%22DUYlEEPTkR_1kujGVuif0etPK8a41fRRHAa0RFVZbEVFUFRrUl8xa3VqR1Z1aWYwZXRQSzhhNDFmUlJIQWEwc2h1%22%2C%22tinker_id%22%3A%22Prod-arm64-v8a-release-13.141.1314110_0812-10-06-09%22%2C%22is_bg_req%22%3A0%2C%22network%22%3A%22wifi%22%2C%22operator%22%3A%22UNKNOWN%22%2C%22abi%22%3A1%7D&curidentity=0&req_time=1771741084302&uniqid=3880525a-bdb9-41fb-b8bc-b38d1addd229&v=13.141
hook_sig ЗЕЛижЕ: V3.0f28a35d5baff6f9c44f199a292bece55
- ВЮЪ§ЗЧГЃГЄЃЌЖјЧвгаurlБрТыЃЌНтТывЛЯТЃЌетРяашвЊЖрДЮНтТыЃЛ
[->] hook_sp ->str= null
hook_sp bArr: batch_method_feed=["method=zpgeek.app.geek.search.cardlist&encryptExpectId=4617621d9b2479b31nZ82tu0FFRSwA~~&expectId=1261694622&filterParams={"cityCode":"101010100","chattedJob":0,"switchCity":0,"labelFilter":{"tags":[{"code":"-1","tag":"ВЛЯо"}],"type":2}}&isFromJd=0&isSupplySearch=false&jids=&maskComType=0&naturalLanguageParam=&noCorrect=0&page=1&prefix=h&pushId=&pushType=&query=python&queryId=&queryTitle=ЫбЫїЗЂЯж&searchType=3&sort=-1&source=1&sugAbKey=M69-GroupA&sugSessionId=1VpO529c1Ho&userIntent=", "method=zpgeek.app.search.listad.query&encryptExpectId=4617621d9b2479b31nZ82tu0FFRSwA~~&filterParams={"cityCode":"101010100","chattedJob":0,"switchCity":0,"labelFilter":{"tags":[{"code":"-1","tag":"ВЛЯо"}],"type":2}}&page=1&query=python&sort=-1"]&client_info={"version":"12","os":"Android","start_time":"1771739823352","resume_time":"1771739823352","channel":"28","model":"google||Pixel 6","dzt":0,"loc_per":0,"uniqid":"3880525a-bdb9-41fb-b8bc-b38d1addd229","oaid":"00000000-0000-0000-0000-000000000000","oaid_honor":"00000000-0000-0000-0000-000000000000","did":"DUYlEEPTkR_1kujGVuif0etPK8a41fRRHAa0RFVZbEVFUFRrUl8xa3VqR1Z1aWYwZXRQSzhhNDFmUlJIQWEwc2h1","tinker_id":"Prod-arm64-v8a-release-13.141.1314110_0812-10-06-09","is_bg_req":0,"network":"wifi","operator":"UNKNOWN","abi":1}&curidentity=0&req_time=1771741084302&uniqid=3880525a-bdb9-41fb-b8bc-b38d1addd229&v=13.141
[<-] hook_sp retval= zwp_NCTRJTSwi3DeUsbkHIGNvU2MDIbyc_aI7pY7DTCAI7RtvzRtOHFgg3UWfOUMTO-UsQF6fAyw-rVGYJBSi6J1KX-FB70JplcewoyOd-dpWuhTl7gbHswG3N8n30lJuDL2_nFt0ONQG0-n42W9F8pD_iIs5mq-AKEi0RN8II4pDgJnH9pbEYKs0O0saFB8dqc6YRZJEJ0Iie7ZpgbwE2wwiQ_MU0Ko9XgrB6fBA_1dNFmp8z_--LNoBZBVyly3CrZasgjpOc5CqKwRiUrLgeb7BHBrymEAHlZDe_BQ8P1lQpGLHh-drdx6NqVHe86G_duGsfA0DoPuKyRaOSH75-PTb9Yub10pIs6LahfPutgSjC2BC09B1CSPjQPp8V2iQL20_x_unCd8sM5VGCTCr3fp9uIE18Rr7h2AMpAfS2xulAGlUjQhDFlyLkNvAWwbXzxVw8ax66GA9lv2bMdJVgs1HyvLF0rTX_ogaeu1FtgtPcGwzQcZ6ePWCAz2ciJdGH_u06080i88ensJkyDQDsnuuq-II60b4YmmKcHvUajXdbx0cDa1ycsUdnY-MDgKcLCbmgrDR5yX2dwcK7j8CzlC0SIQciE6Uc0SmPvpotX-eMKVGNlvblAg-XhXapAGzh7FwgfkDhGobrDNJ7lrCGu7IsKm-LAmuBPJUwV5QX0rWlkMM2xbo4UF1CskcpwwdPGEmg5eNxblPz3twdT_J6UqTMf63ORXTdROYuRT5D12saAMLm6gcjeaSk06KWura_DeVO_10mNKdk7yPf1rtwWuiG2WVwGKZLm7Oab_6NREKqkHMiXBc0d0r7hIWoC0Hi1aAB-h1boc91JBaZYLMN1tq3QWhDr_E0MrsjIHAO_jLhC56IcCQIYg44lmg3nvwrcbpqr6LzM6484_mTRummQWwOr5QFbqFtucP_elAVo5oNqbL_UrpbNjpcd_IdRn1wN4ak9HgBKWyXZvz1t-DNAGzA-EY-P_oP5etPcmoeO5C4Mt8eU-w_HO4aJljV0CQU_KnxyKB9Jfo_7o3E61W38LSlX6vxfaMQtmVDNjzERTXoMK73Q0KnWdd9RQEwn2bL1f9ruh2ngZvUG4PRaFp5w9dMq2-u-VU-0yjIJN81kbWcvHDoEVtT5MdubBYy3uNhetDoKY1NiiOFK7RWsDSB_K_a1ULaxaW2mun3Q4Qt8bkz4QyNwTF146dPhJxzrDQpx0ExNMvmBQRi7I9H-DY-ZJBLSIBn8tOSeb-2nWWN2cP_dl2Li9vk9jk5megfnb8LplyyA6WfD2MXhjYkVvUTgJ403oy0bYGYE7An3wOGOkmmK2Ip84EYPnKfcuMsihH-QUfUPzDGX-QWFzdj9X8GoEwevatOO0itUY7aMfLcW9icX0pziGDXIGv1rCo5xZSteXjc7besqHQpAxSkVKeqa2KQt33XmCjeJgE-Oh5X_ENG4bH7q5I9HLaLPBox7hSSUbq9NHay29dAZCPwujW9JnLsrm8BdACCpjO62Zl7IkKgoQ3ZgmQIkk1PYqUWSoOYMXQHCxL9SYRE4QcMs3UcUdw6_FWXokQalqSgqEwQfI0ZV4VqUkgf7qek59tggzKAA7N1eInXA_HXqX0wVNVznyrL0hkKXx50fmKxV7WrwitKRg2qXLr1I22-mhekVR8QUh-BiAog0Lqhf2mej1esVdBiqRq2CPmMJeN8I~
[->] hook_sig ->str= null
hook_sig bArr: /api/batch/batchRunV2batch_method_feed=["method=zpgeek.app.geek.search.cardlist&encryptExpectId=4617621d9b2479b31nZ82tu0FFRSwA~~&expectId=1261694622&filterParams={"cityCode":"101010100","chattedJob":0,"switchCity":0,"labelFilter":{"tags":[{"code":"-1","tag":"ВЛЯо"}],"type":2}}&isFromJd=0&isSupplySearch=false&jids=&maskComType=0&naturalLanguageParam=&noCorrect=0&page=1&prefix=h&pushId=&pushType=&query=python&queryId=&queryTitle=ЫбЫїЗЂЯж&searchType=3&sort=-1&source=1&sugAbKey=M69-GroupA&sugSessionId=1VpO529c1Ho&userIntent=", "method=zpgeek.app.search.listad.query&encryptExpectId=4617621d9b2479b31nZ82tu0FFRSwA~~&filterParams={"cityCode":"101010100","chattedJob":0,"switchCity":0,"labelFilter":{"tags":[{"code":"-1","tag":"ВЛЯо"}],"type":2}}&page=1&query=python&sort=-1"]&client_info={"version":"12","os":"Android","start_time":"1771739823352","resume_time":"1771739823352","channel":"28","model":"google||Pixel 6","dzt":0,"loc_per":0,"uniqid":"3880525a-bdb9-41fb-b8bc-b38d1addd229","oaid":"00000000-0000-0000-0000-000000000000","oaid_honor":"00000000-0000-0000-0000-000000000000","did":"DUYlEEPTkR_1kujGVuif0etPK8a41fRRHAa0RFVZbEVFUFRrUl8xa3VqR1Z1aWYwZXRQSzhhNDFmUlJIQWEwc2h1","tinker_id":"Prod-arm64-v8a-release-13.141.1314110_0812-10-06-09","is_bg_req":0,"network":"wifi","operator":"UNKNOWN","abi":1}&curidentity=0&req_time=1771741084302&uniqid=3880525a-bdb9-41fb-b8bc-b38d1addd229&v=13.141
hook_sig ЗЕЛижЕ: V3.0f28a35d5baff6f9c44f199a292bece55
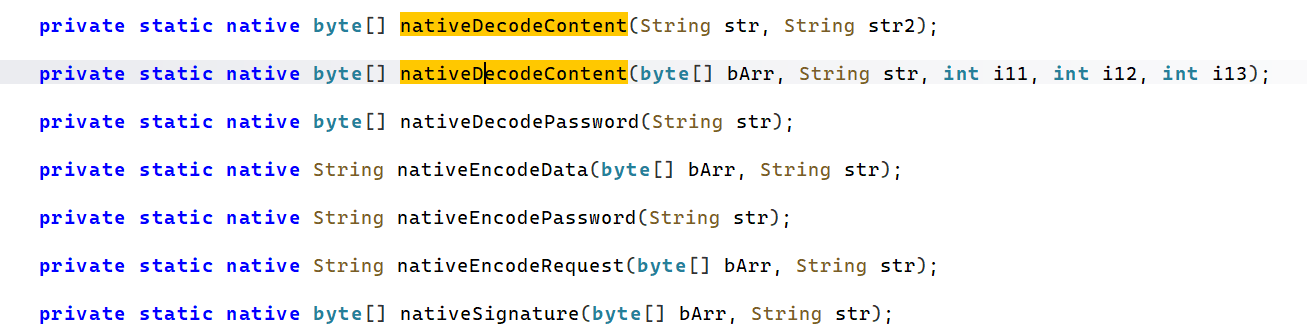
- МђЕЅЖдБШПЩвдЗЂЯжЃЌСНИіЗНЗЈЕФbArrЦфЪЕЪЧвЛбљЕФЃЌжЛЪЧsigЕФЖрСЫвЛИіЕБЧАНгПкЦДдкзюЧАУцЃЌЖјЧвСНИізжЗћДЎЖМЪЧnullЃЌЫљвдетСНИіВЮЪ§УшЪіЕФЖЋЮїЪЧвЛбљЕФЃЌжЛЪЧаЮЪНВЛвЛбљЃЛ
- КѓајunidbgжїЖЏЕїгУЕФЪБКђМЧЕУДЋдЪМЕФВЮЪ§ЃЌетРяжЛЪЧЮЊСЫЗНБуПДЖјвбЃЌЯрЖдРДЫЕЃЌЯьгІЕФНтУмгІЕБвВЪЧетИіЮЛжУВХЖдЃЛ
- ЮвУЧЫГБувВАбЫќЕФКЏЪ§евГіРДЃЌЮвЪЧБШНЯЦЋЯђгкЫќУЧЖМдкЭЌвЛИіsoЕФЃЌЖјЧвИННќвВгаРрЫЦЕФКЏЪ§ЃЛ
- ЮвВТВтЪЧбЁжаЕФетСНИіКЏЪ§жЎвЛЃЌЮвУЧЖМhookЩЯЪдЪдЃЌПДПДЪЧВЛЪЧЫћУЧжЎвЛЃЛ
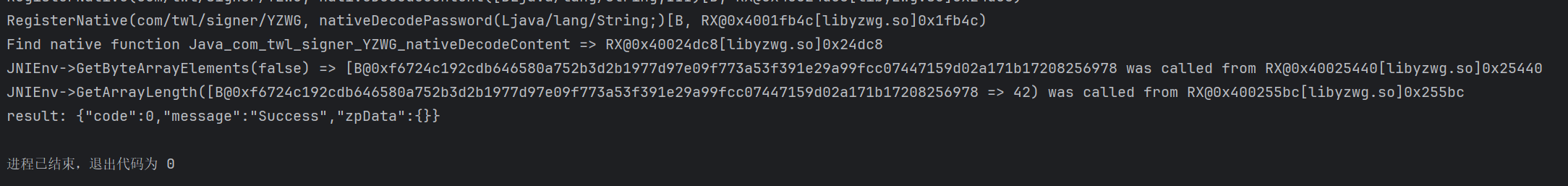
[->] nativeDecodeContent is called!
->bArr= -49,10,127,52,36,-47,37,52,-80,-117,112,-34,-61,-15,-28ЁЄЁЄЁЄЪЁТдВПЗжЪ§ОнЁЄЁЄЁЄ,123,-113,-3,-62
->str= null
->i11= 0
->i12= 1
->i13= 2
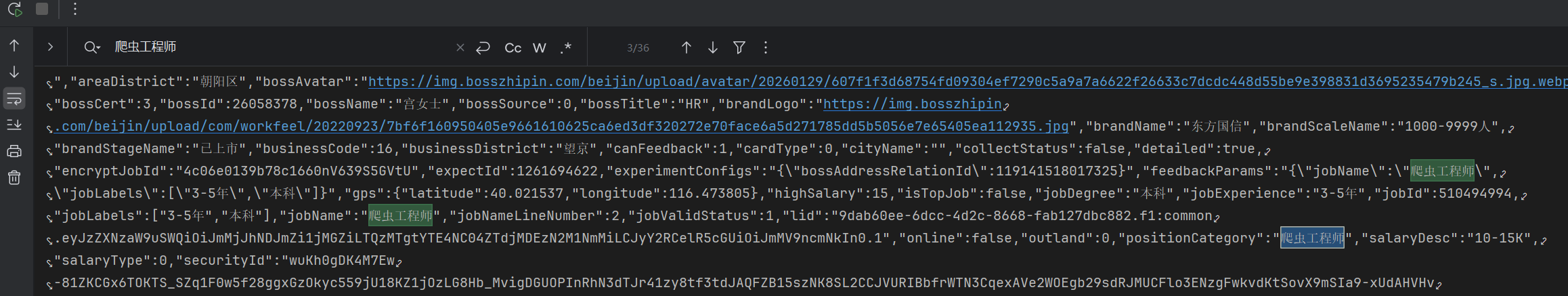
nativeDecodeContent retval: {"code":0,"message":"Success","zpData":{"zpgeek.app.geek.search.cardlist":{"code":0,"message":"Success","zpData":{"askAiEntrance":false,"cardList":[{"brandCardStyle":0,"hasMore":true,"jobCardStyle":0,"positionSearchCardList":[{"afterNameIcons":[{"height":48,"url":"https://img.bosszhipin.com/beijin/icon/20250107/b0d69dde1b861aef40e116820c982b289df0490b3b48e06fecc269e8d551a6fe1adc516614a77077.png","width":48}],"areaBusinessName":"ЭћОЉ","areaDistrict":"ГЏбєЧј","bossOnline":{"detailOnlinЁЄЁЄЁЄЁЄЪЁТдВПЗжЪ§ОнЁЄЁЄЁЄЁЄ"zpData":{"listAds":[]}}}}
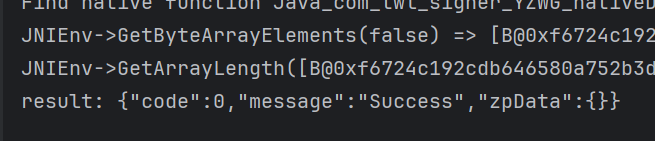
- ПЩвдЗЂЯжЃЌШЗЪЕзпСЫЃЌЖјЧвЪЧВЮЪ§БШНЯЖрЕФФЧвЛИіКЏЪ§ЃЌЕНетРяШ§ИіКЏЪ§ЮвУЧЖМЖЈЮЛКУСЫЃЛКѓајПЊЪМЗжЮіОпЬхЕФЫуЗЈЃЌЯШАбunidbgХмЭЈЃЛетРядкunidbgЕїгУЕФЪБКђзЂвтетМИИіintВЮЪ§ЃЌгааЉЪБКђЕкШ§ИіВЂВЛЪЧ2ЃЌздМКзЂвтОЭКУСЫЃЛ
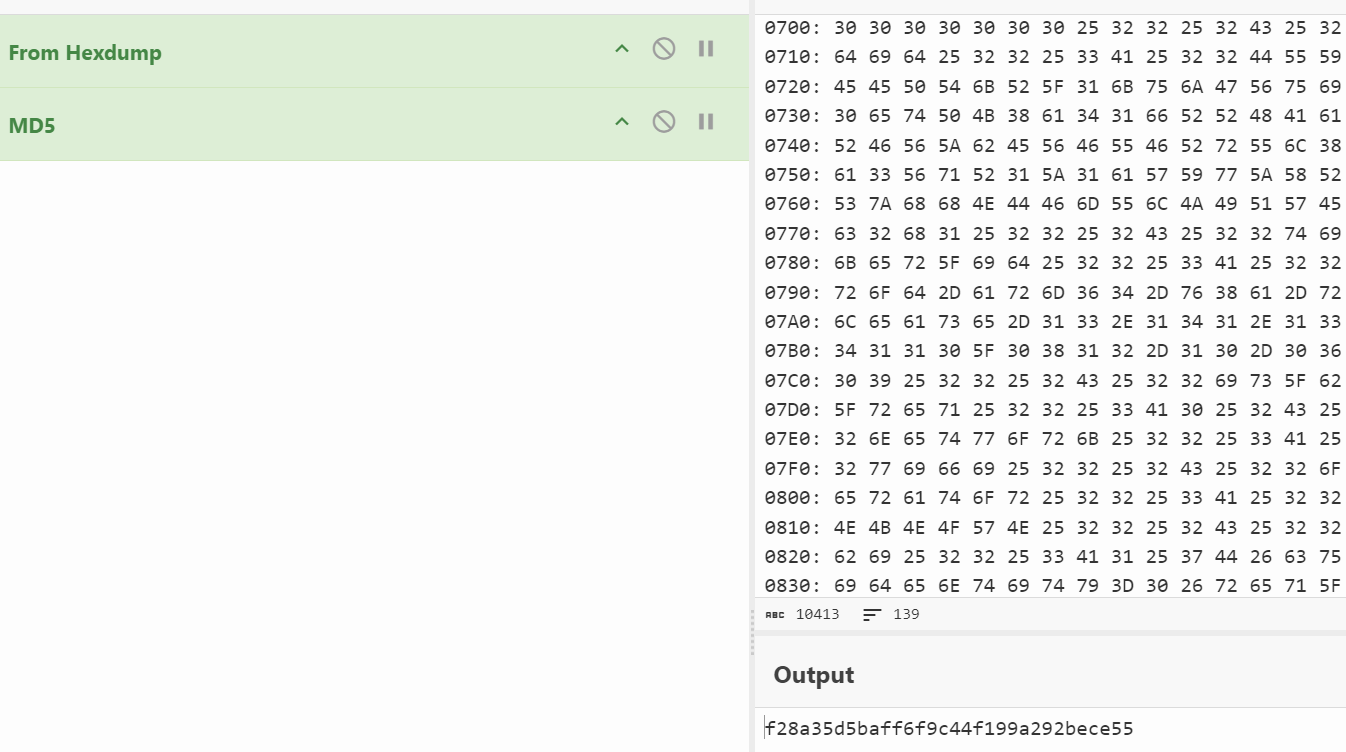
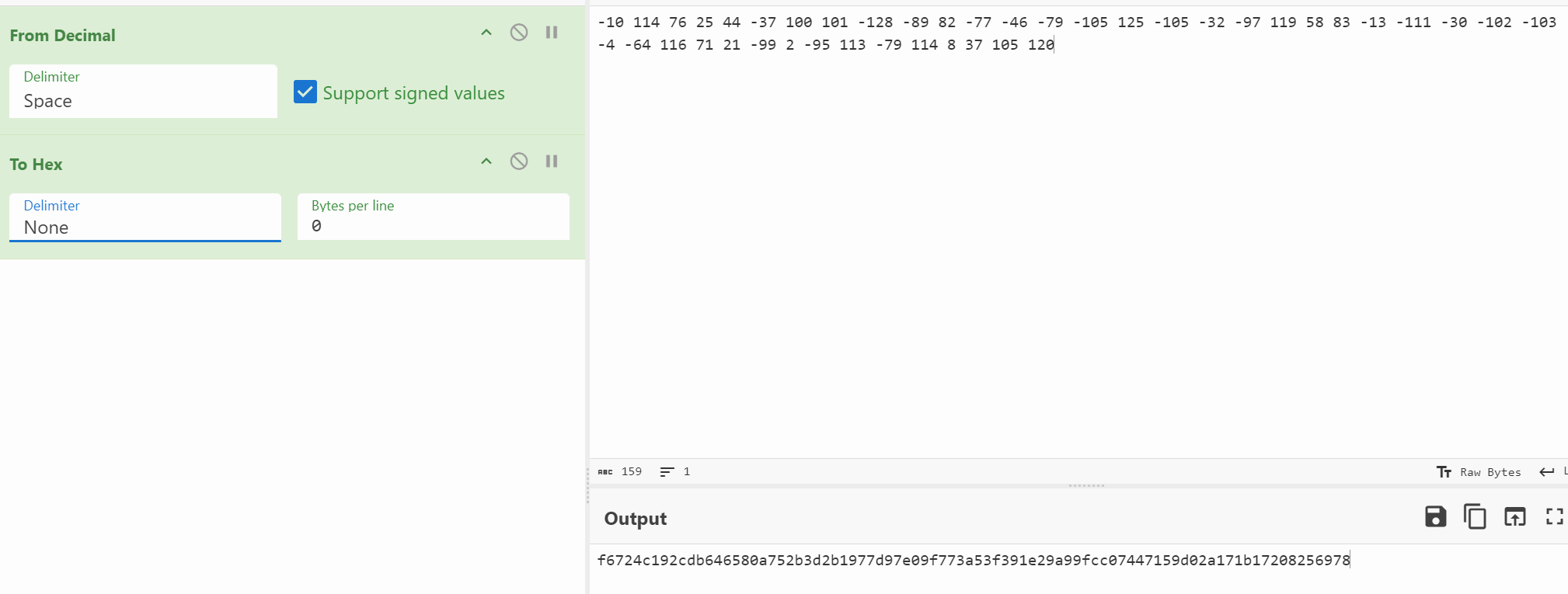
- ЖдСЫЃЌbArrетИіВЮЪ§ОЭЪЧЗЕЛижЕЃЌПЩвдШЅcyberchefВтЪдвЛЯТЃЌЪЧвЛбљЕФЃЛ
3. ФЃФтжДаа
package com.Samples.boss;
import com.github.unidbg.AndroidEmulator;
import com.github.unidbg.Emulator;
import com.github.unidbg.Module;
import com.github.unidbg.arm.backend.Unicorn2Factory;
import com.github.unidbg.arm.context.RegisterContext;
import com.github.unidbg.debugger.BreakPointCallback;
import com.github.unidbg.file.FileResult;
import com.github.unidbg.file.IOResolver;
import com.github.unidbg.linux.android.AndroidEmulatorBuilder;
import com.github.unidbg.linux.android.AndroidResolver;
import com.github.unidbg.linux.android.dvm.*;
import com.github.unidbg.linux.android.dvm.api.ClassLoader;
import com.github.unidbg.memory.Memory;
import com.github.unidbg.pointer.UnidbgPointer;
import com.github.unidbg.utils.Inspector;
import java.io.File;
import java.io.FileNotFoundException;
import java.io.FileOutputStream;
import java.io.PrintStream;
import java.util.ArrayList;
import java.util.List;
public class YZWG extends AbstractJni implements IOResolver {
public static AndroidEmulator emulator;
public static Memory memory;
public static VM vm;
public static Module module;
@Override
public FileResult resolve(Emulator emulator, String pathname, int oflags) {
System.out.println("sana file open-->>" + pathname);
return null;
}
public YZWG() {
emulator = AndroidEmulatorBuilder
.for64Bit()
.setProcessName("com.hpbr.bosszhipin")
.addBackendFactory(new Unicorn2Factory(false))
.build();
// ЮФМўЗУЮЪ зЂвтетРяЕФДІРэЃЌМгЩЯетвЛОф
emulator.getSyscallHandler().addIOResolver(this);
memory = emulator.getMemory();
memory.setLibraryResolver(new AndroidResolver(23));
vm = emulator.createDalvikVM(new File("src/test/java/com/Samples/boss/files/BOSSжБЦИv13.141.apk"));
// ащФтФЃПщ ЬэМгетИіОЭПЩвд
// new AndroidModule(emulator, vm).register(memory);
vm.setJni(this);
vm.setVerbose(true);
DalvikModule dm = vm.loadLibrary(new File("src/test/java/com/Samples/boss/files/libyzwg.so"), true);
module = dm.getModule();
dm.callJNI_OnLoad(emulator);
}
public static void main(String[] args) {
YZWG demo = new YZWG();
}
}
java.lang.UnsupportedOperationException: com/twl/signer/YZWG->gContext:Landroid/content/Context;
at com.github.unidbg.linux.android.dvm.AbstractJni.getStaticObjectField(AbstractJni.java:103)
at com.github.unidbg.linux.android.dvm.AbstractJni.getStaticObjectField(AbstractJni.java:53)
@Override
public DvmObject<?> getStaticObjectField(BaseVM vm, DvmClass dvmClass, String signature) {
switch (signature){
case "com/twl/signer/YZWG->gContext:Landroid/content/Context;":{
return vm.resolveClass("android/content/Context").newObject(signature);
}
}
return super.getStaticObjectField(vm, dvmClass, signature);
}
java.lang.UnsupportedOperationException: android/content/pm/PackageManager->getPackagesForUid(I)[Ljava/lang/String;
at com.github.unidbg.linux.android.dvm.AbstractJni.callObjectMethod(AbstractJni.java:937)
at com.github.unidbg.linux.android.dvm.AbstractJni.callObjectMethod(AbstractJni.java:871)
- етИівВжБНгВЙЃЌЪЕМЪЩЯЪЧЛёШЁАќУћЃЌжБНгЗЕЛивВЮДГЂВЛПЩЃЛ
@Override
public DvmObject<?> callObjectMethod(BaseVM vm, DvmObject<?> dvmObject, String signature, VarArg varArg) {
switch (signature){
case "android/content/pm/PackageManager->getPackagesForUid(I)[Ljava/lang/String;":{
System.out.println("[+]sana getPackagesForUid uid-->>" + varArg.getIntArg(0));
return new ArrayObject(new StringObject(vm, vm.getPackageName()));
}
}
return super.callObjectMethod(vm, dvmObject, signature, varArg);
}
java.lang.UnsupportedOperationException: java/lang/String->hashCode()I
at com.github.unidbg.linux.android.dvm.AbstractJni.callIntMethod(AbstractJni.java:969)
at com.github.unidbg.linux.android.dvm.AbstractJni.callIntMethod(AbstractJni.java:942)
- етИіЛёШЁвЛИіhashcodeЃЌКѓајПЩФмЛсгУЩЯЃЌПЩвдСєвтвЛЯТЃЛ
@Override
public int callIntMethod(BaseVM vm, DvmObject<?> dvmObject, String signature, VarArg varArg) {
switch (signature){
case "java/lang/String->hashCode()I":{
int value = dvmObject.getValue().hashCode();
return value;
}
}
return super.callIntMethod(vm, dvmObject, signature, varArg);
}
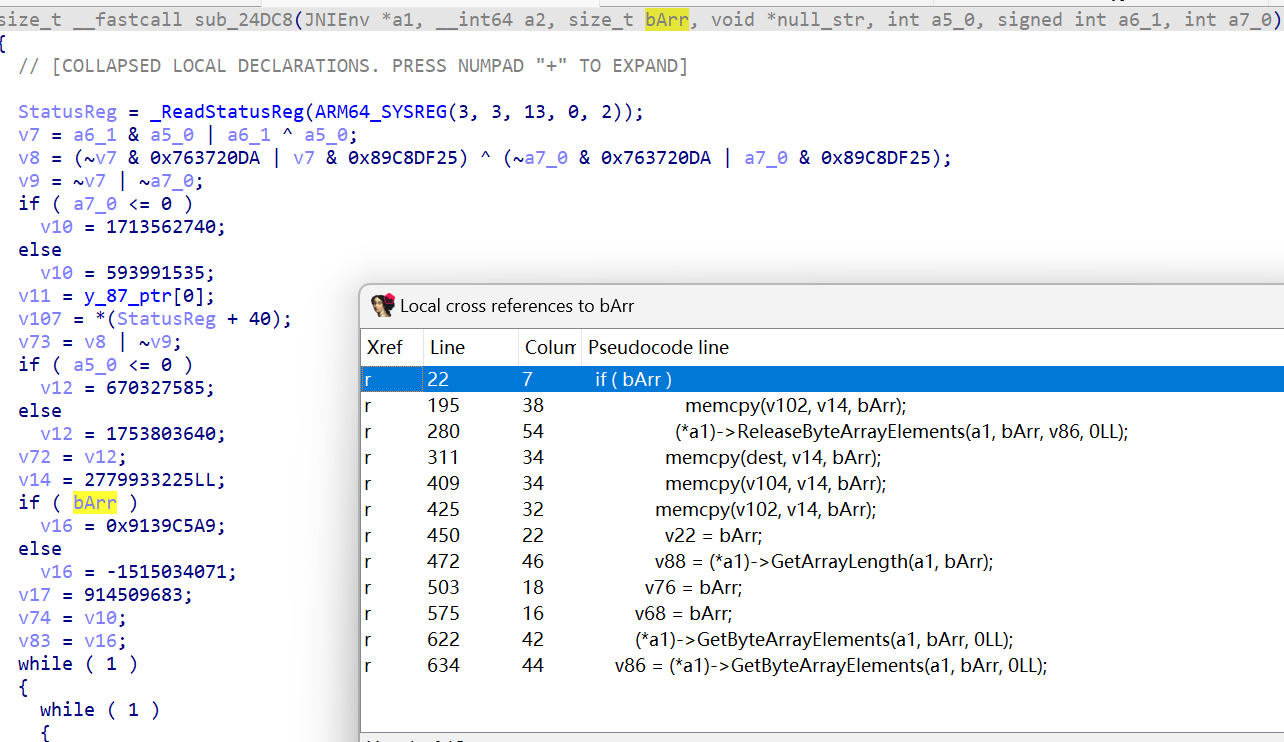
- ЕНетРяОЭУЛгаЛЗОГЮЪЬтСЫЃЌПЩвдПЊЪМcallСЫЃЛ
RegisterNative(com/twl/signer/YZWG, nativeEncodePassword(Ljava/lang/String;)Ljava/lang/String;, RX@0x4001f650[libyzwg.so]0x1f650)
RegisterNative(com/twl/signer/YZWG, nativeEncodeData([BLjava/lang/String;)Ljava/lang/String;, RX@0x400200c0[libyzwg.so]0x200c0)
RegisterNative(com/twl/signer/YZWG, nativeEncodeRequest([BLjava/lang/String;)Ljava/lang/String;, RX@0x400209a4[libyzwg.so]0x209a4)
RegisterNative(com/twl/signer/YZWG, nativeSignature([BLjava/lang/String;)[B, RX@0x40021864[libyzwg.so]0x21864)
RegisterNative(com/twl/signer/YZWG, nativeDecodeContent(Ljava/lang/String;Ljava/lang/String;)[B, RX@0x40022ad0[libyzwg.so]0x22ad0)
RegisterNative(com/twl/signer/YZWG, nativeDecodeContent([BLjava/lang/String;III)[B, RX@0x40024dc8[libyzwg.so]0x24dc8)
RegisterNative(com/twl/signer/YZWG, nativeDecodePassword(Ljava/lang/String;)[B, RX@0x4001fb4c[libyzwg.so]0x1fb4c)
- ВЮЪ§ОЭгУжЎЧАИјГіЕФФЧвЛИіАЩЃЛвЛЙВСНИіВЮЪ§ЃЌетРягУapiРДЕїгУЃЌБШНЯЗНБуЃЛ
public void call_sig() {
byte[] bArr = "/api/batch/batchRunV2batch_method_feed=%5B%22method%3Dzpgeek.app.geek.search.cardlist%26encryptExpectId%3D4617621d9b2479b31nZ82tu0FFRSwA%257E%257E%26expectId%3D1261694622%26filterParams%3D%257B%2522cityCode%2522%253A%2522101010100%2522%252C%2522chattedJob%2522%253A0%252C%2522switchCity%2522%253A0%252C%2522labelFilter%2522%253A%257B%2522tags%2522%253A%255B%257B%2522code%2522%253A%2522-1%2522%252C%2522tag%2522%253A%2522%25E4%25B8%258D%25E9%2599%2590%2522%257D%255D%252C%2522type%2522%253A2%257D%257D%26isFromJd%3D0%26isSupplySearch%3Dfalse%26jids%3D%26maskComType%3D0%26naturalLanguageParam%3D%26noCorrect%3D0%26page%3D1%26prefix%3Dh%26pushId%3D%26pushType%3D%26query%3Dpython%26queryId%3D%26queryTitle%3D%25E6%2590%259C%25E7%25B4%25A2%25E5%258F%2591%25E7%258E%25B0%26searchType%3D3%26sort%3D-1%26source%3D1%26sugAbKey%3DM69-GroupA%26sugSessionId%3D1VpO529c1Ho%26userIntent%3D%22%2C+%22method%3Dzpgeek.app.search.listad.query%26encryptExpectId%3D4617621d9b2479b31nZ82tu0FFRSwA%257E%257E%26filterParams%3D%257B%2522cityCode%2522%253A%2522101010100%2522%252C%2522chattedJob%2522%253A0%252C%2522switchCity%2522%253A0%252C%2522labelFilter%2522%253A%257B%2522tags%2522%253A%255B%257B%2522code%2522%253A%2522-1%2522%252C%2522tag%2522%253A%2522%25E4%25B8%258D%25E9%2599%2590%2522%257D%255D%252C%2522type%2522%253A2%257D%257D%26page%3D1%26query%3Dpython%26sort%3D-1%22%5D&client_info=%7B%22version%22%3A%2212%22%2C%22os%22%3A%22Android%22%2C%22start_time%22%3A%221771739823352%22%2C%22resume_time%22%3A%221771739823352%22%2C%22channel%22%3A%2228%22%2C%22model%22%3A%22google%7C%7CPixel+6%22%2C%22dzt%22%3A0%2C%22loc_per%22%3A0%2C%22uniqid%22%3A%223880525a-bdb9-41fb-b8bc-b38d1addd229%22%2C%22oaid%22%3A%2200000000-0000-0000-0000-000000000000%22%2C%22oaid_honor%22%3A%2200000000-0000-0000-0000-000000000000%22%2C%22did%22%3A%22DUYlEEPTkR_1kujGVuif0etPK8a41fRRHAa0RFVZbEVFUFRrUl8xa3VqR1Z1aWYwZXRQSzhhNDFmUlJIQWEwc2h1%22%2C%22tinker_id%22%3A%22Prod-arm64-v8a-release-13.141.1314110_0812-10-06-09%22%2C%22is_bg_req%22%3A0%2C%22network%22%3A%22wifi%22%2C%22operator%22%3A%22UNKNOWN%22%2C%22abi%22%3A1%7D&curidentity=0&req_time=1771741084302&uniqid=3880525a-bdb9-41fb-b8bc-b38d1addd229&v=13.141".getBytes();
// ЕїгУОВЬЌnativeЗНЗЈ
DvmObject<?> result = YZWG.callStaticJniMethodObject(
emulator,
"nativeSignature([BLjava/lang/String;)[B",
bArr,
null
);
//ЛёШЁВЂЗЕЛиНсЙћ
byte[] res = (byte[]) result.getValue();
System.out.println("[+]call_sig result:" + new String(res, StandardCharsets.UTF_8));
}
- жБНгОЭгаНсЙћЃЌЖјЧвКЭзЅАќЪЧЖдЕУЩЯЕФЃЛ
[+]call_sig result:
V3.0f28a35d5baff6f9c44f199a292bece55
зЅАќЃКV3.0f28a35d5baff6f9c44f199a292bece55
public void call_sp(){
byte[] bArr1 = "batch_method_feed=%5B%22method%3Dzpgeek.app.geek.search.cardlist%26encryptExpectId%3D4617621d9b2479b31nZ82tu0FFRSwA%257E%257E%26expectId%3D1261694622%26filterParams%3D%257B%2522cityCode%2522%253A%2522101010100%2522%252C%2522chattedJob%2522%253A0%252C%2522switchCity%2522%253A0%252C%2522labelFilter%2522%253A%257B%2522tags%2522%253A%255B%257B%2522code%2522%253A%2522-1%2522%252C%2522tag%2522%253A%2522%25E4%25B8%258D%25E9%2599%2590%2522%257D%255D%252C%2522type%2522%253A2%257D%257D%26isFromJd%3D0%26isSupplySearch%3Dfalse%26jids%3D%26maskComType%3D0%26naturalLanguageParam%3D%26noCorrect%3D0%26page%3D1%26prefix%3Dh%26pushId%3D%26pushType%3D%26query%3Dpython%26queryId%3D%26queryTitle%3D%25E6%2590%259C%25E7%25B4%25A2%25E5%258F%2591%25E7%258E%25B0%26searchType%3D3%26sort%3D-1%26source%3D1%26sugAbKey%3DM69-GroupA%26sugSessionId%3D1VpO529c1Ho%26userIntent%3D%22%2C+%22method%3Dzpgeek.app.search.listad.query%26encryptExpectId%3D4617621d9b2479b31nZ82tu0FFRSwA%257E%257E%26filterParams%3D%257B%2522cityCode%2522%253A%2522101010100%2522%252C%2522chattedJob%2522%253A0%252C%2522switchCity%2522%253A0%252C%2522labelFilter%2522%253A%257B%2522tags%2522%253A%255B%257B%2522code%2522%253A%2522-1%2522%252C%2522tag%2522%253A%2522%25E4%25B8%258D%25E9%2599%2590%2522%257D%255D%252C%2522type%2522%253A2%257D%257D%26page%3D1%26query%3Dpython%26sort%3D-1%22%5D&client_info=%7B%22version%22%3A%2212%22%2C%22os%22%3A%22Android%22%2C%22start_time%22%3A%221771739823352%22%2C%22resume_time%22%3A%221771739823352%22%2C%22channel%22%3A%2228%22%2C%22model%22%3A%22google%7C%7CPixel+6%22%2C%22dzt%22%3A0%2C%22loc_per%22%3A0%2C%22uniqid%22%3A%223880525a-bdb9-41fb-b8bc-b38d1addd229%22%2C%22oaid%22%3A%2200000000-0000-0000-0000-000000000000%22%2C%22oaid_honor%22%3A%2200000000-0000-0000-0000-000000000000%22%2C%22did%22%3A%22DUYlEEPTkR_1kujGVuif0etPK8a41fRRHAa0RFVZbEVFUFRrUl8xa3VqR1Z1aWYwZXRQSzhhNDFmUlJIQWEwc2h1%22%2C%22tinker_id%22%3A%22Prod-arm64-v8a-release-13.141.1314110_0812-10-06-09%22%2C%22is_bg_req%22%3A0%2C%22network%22%3A%22wifi%22%2C%22operator%22%3A%22UNKNOWN%22%2C%22abi%22%3A1%7D&curidentity=0&req_time=1771741084302&uniqid=3880525a-bdb9-41fb-b8bc-b38d1addd229&v=13.141".getBytes();
//ЕїгУОВЬЌnativeЗНЗЈ
DvmObject<?> result = YZWG.callStaticJniMethodObject(
emulator,
"nativeEncodeRequest([BLjava/lang/String;)Ljava/lang/String;",
bArr1,
null
);
//ЛёШЁВЂЗЕЛиНсЙћ
String res = (String) result.getValue();
System.out.println("[+]call_sp result:" + res);
}
- ЬЋГЄСЫЃЌВЛаДГіНсЙћСЫЃЌвВЪЧВЛгУдйВЙЛЗОГЃЌжБНгОЭгаНсЙћЃЌЖјЧвКЭзЅАќЖдЕУЩЯЃЛ
- ЫГБуАбЗЕЛижЕЕФЕїгУвВаДСЫЃЌетИівВВЛашвЊВЙЛЗОГЃЌЕЋЪЧЪ§ОнЬЋеМЦЊЗљСЫЃЌВЛаДСЫЃЛВЛЙ§етРяашвЊзЂвтМИИіЕуЃЌЪзЯШЪЧдЪМЗЕЛижЕЬЋГЄСЫЃЌЮвУЧашвЊбАевЖЬвЛЕуЕФРДЕїгУЃЛВЂЧвВЛЭЌЕФГЄЖШзюКѓвЛИіintВЮЪ§ЪЧВЛвЛбљЕФЃЛ
public void decode_response() {
byte[] bArr = {-10, 114, 76, 25, 44, -37, 100, 101, -128, -89, 82, -77, -46, -79, -105, 125, -105, -32, -97, 119, 58, 83, -13, -111, -30, -102, -103, -4, -64, 116, 71, 21, -99, 2, -95, 113, -79, 114, 8, 37, 105, 120};
int i11 = 0;
int i12 = 1;
int i13 = 0; // ЖЬЕФЪЧ0 ГЄЕФЪЧ2
//ЕїгУОВЬЌnativeЗНЗЈ
DvmObject<?> result = YZWG.callStaticJniMethodObject(
emulator,
"nativeDecodeContent([BLjava/lang/String;III)[B",
bArr,
null,
i11,
i12,
i13
);
//ЛёШЁВЂЗЕЛиНсЙћ
byte[] res3 = (byte[]) result.getValue();
System.out.println("result: " + new String(res3));
}
- ЕНетРяЛљДЁЕФзМБИОЭЖМзіКУСЫЃЌПЩвдПЊЪМЫуЗЈЗжЮіСЫЃЛ
4. ЫуЗЈЗжЮі
4.1 sig
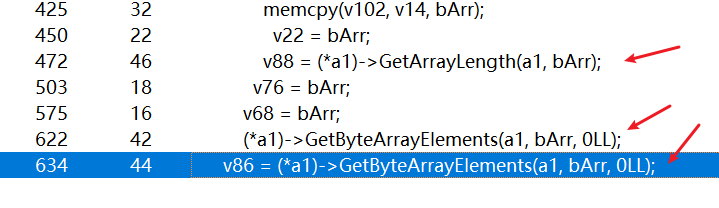
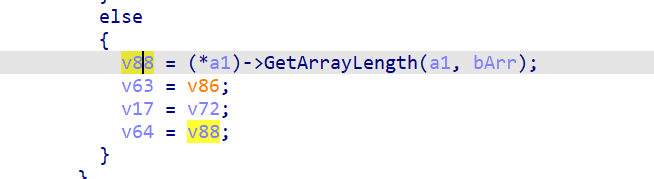
- ЯШРДЗжЮіsigВЮЪ§ЃЌАбЦфЫћСНИіЕїгУЯШЭЃСЫЃЌРЯЙцОиЃЌДђПЊmemcpyЕФhookЃЛВЂЧвАбУмЮФНсЙћзЊГЩhexdumpЃЌЗНБуЗжЮіЃЛ
00000000 66 32 38 61 33 35 64 35 62 61 66 66 36 66 39 63 |f28a35d5baff6f9c|
00000010 34 34 66 31 39 39 61 32 39 32 62 65 63 65 35 35 |44f199a292bece55|
>-----------------------------------------------------------------------------<
[16:19:06 757]ФПБъ: 40713060 РДдД(жївЊзЗетРя): bfffef1a lr 40578dc4, md5=3667f6a0c97490758d7dc9659d01ea34, hex=6632
size: 2
0000: 66 32 f2
^-----------------------------------------------------------------------------^
>-----------------------------------------------------------------------------<
[16:19:06 758]ФПБъ: 40713062 РДдД(жївЊзЗетРя): bfffef1a lr 40578dc4, md5=8edd87c407c4a1732e4924598236e319, hex=3861
size: 2
0000: 38 61 8a
^-----------------------------------------------------------------------------^
>-----------------------------------------------------------------------------<
[16:19:06 758]ФПБъ: 40713064 РДдД(жївЊзЗетРя): bfffef1a lr 40578dc4, md5=1c383cd30b7c298ab50293adfecb7b18, hex=3335
size: 2
0000: 33 35 35
^-----------------------------------------------------------------------------^
- ПЩвдЗЂЯжвЛаЉжыЫПТэМЃЃЌФЧПЩвдШЅеввЛЯТаДШыЮЛжУЕФаХЯЂЃЛ
emulator.traceWrite(0xbfffef1aL, 0xbfffef1aL + 0x10);
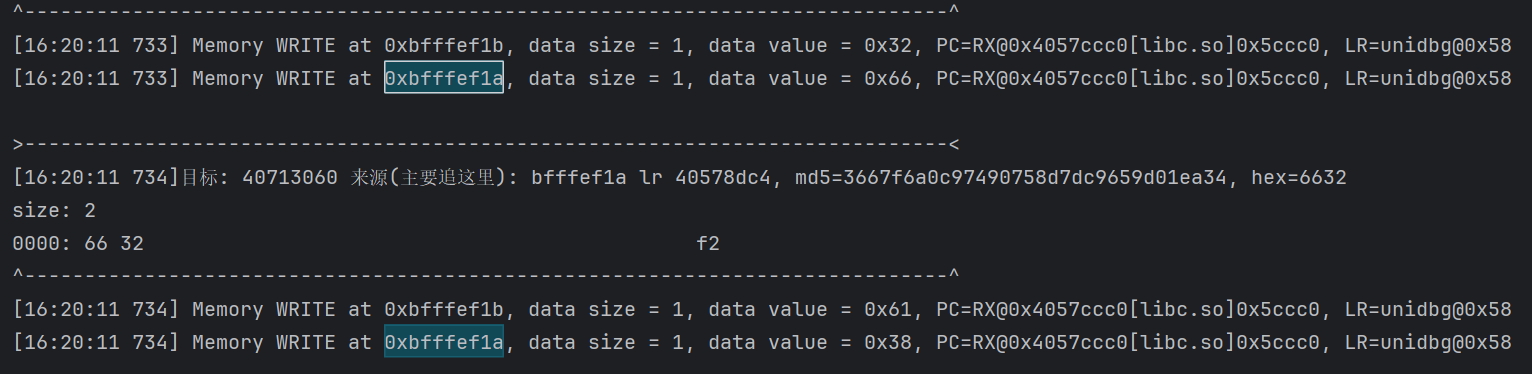
- pcЪЧlibcЕФКЏЪ§ЃЌетжжвЛАуОЭВЛЬЋКУМЬајзЗСЫЃЌПЩвдДђПЊunidbgЕФlibcПДПДЪЧЪВУДКЏЪ§ЃЌЫќЪЕМЪЩЯЪЧвЛИі_vfprintfКЏЪ§ЃЛ
- етРяашвЊСэБйѕшОЖЃЌЛиШЅПДзюКѓЕФШежОЃЛ
JNIEnv->SetByteArrayRegion([B@0x000000000000000000000000000000000000000000000000000000000000000000000000, 0, 36, RW@0x40713090) was called from RX@0x40021fdc[libyzwg.so]0x21fdc
[+]call_sig result:V3.0f28a35d5baff6f9c44f199a292bece55
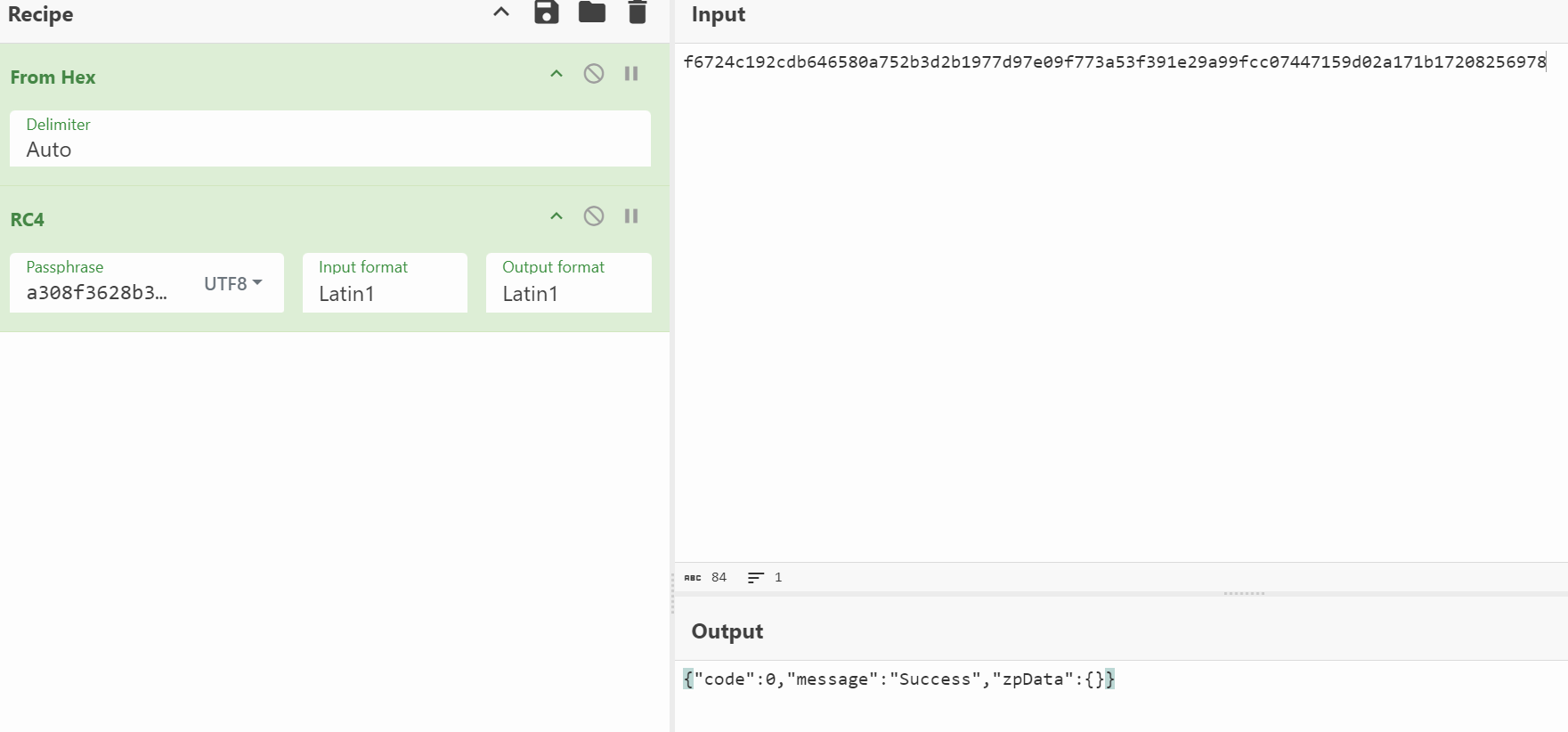
- ШЅзЗвЛЯТ0x21fdcетИіЮЛжУЃЛ
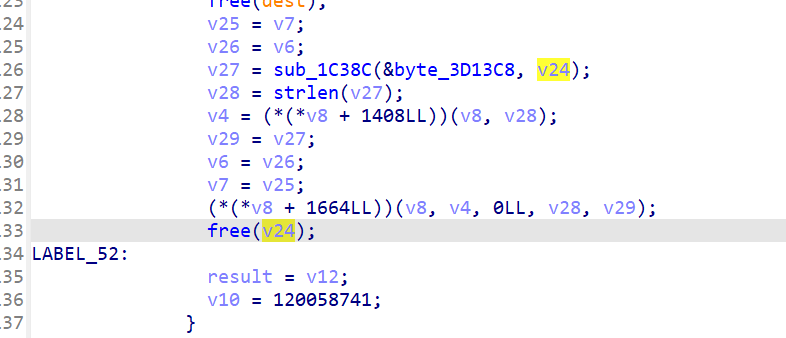
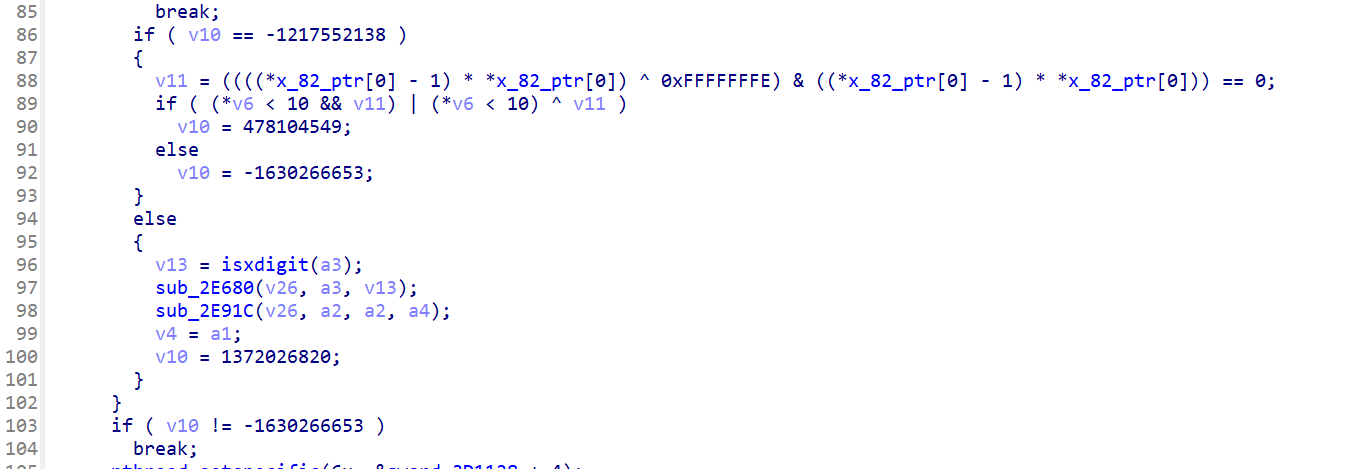
- ЕквЛблШЗЪЕПДВЛГіРДЪВУДЃЌЕЋетРяЮвУЧзЗЕФЪЧSetByteArrayRegionЃЌетРяВЂУЛгаПДЕНЃЌФЧУДv8ЛљБОЩЯОЭЪЧjnienvЃЌ+1664ЪЕМЪЩЯЪЧЦЋвЦЃЌЮвУЧИФвЛЯТРраЭОЭПЩвдПДГіРДСЫЃЛ
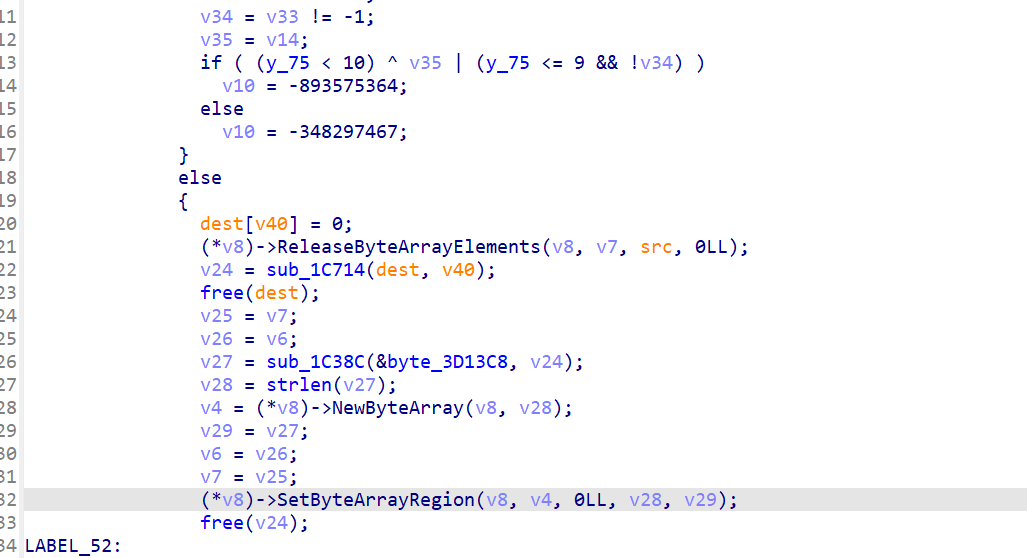
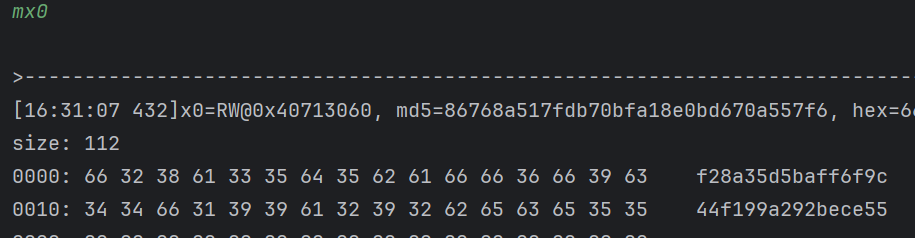
- зюКѓвЛИіВЮЪ§ЪЧдДЪ§ОнжИеыЃЌЫљвдШЅевЫќЃЌv29гжЕШгкv27ЃЌЫљвдШЅhook sub_1C38CетИіКЏЪ§ЃЛЫћвЛЙВгаСНИіВЮЪ§ЃЛ
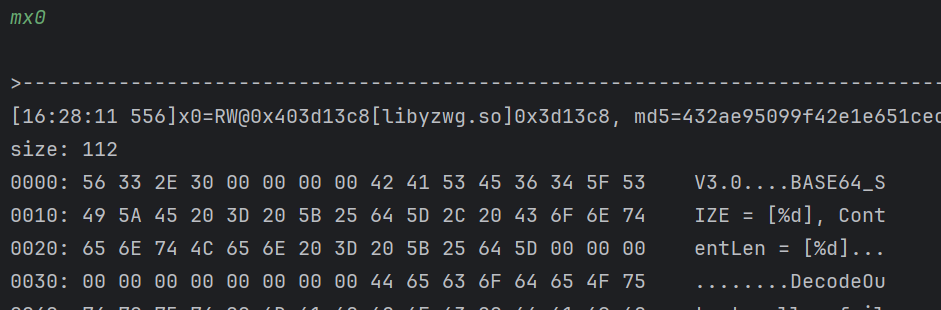
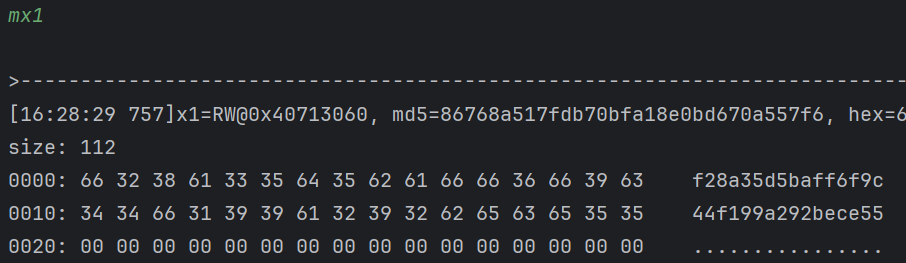
- ВЮЪ§1ПДЦ№РДгІИУЪЧЧАзКЃЌВЮЪ§2дђЪЧНсЙћЃЌФЧЛЙашвЊМЬајзЗЃЌвВОЭЪЧШЅhook 0x1C714етИіКЏЪ§ЃЛЫќвВЪЧСНИіВЮЪ§ЃЌВЂЧвЮвУЧашвЊШЅПДЫќЕФЗЕЛижЕЃЛ
mx0 0x8a6
>-----------------------------------------------------------------------------<
[16:30:02 318]x0=RW@0x40719000, hex=2f617069ЁЄЁЄЁЄЁЄЁЄ261746368
size: 2214
0000: 2F 61 70 69 2F 62 61 74 63 68 2F 62 61 74 63 68 /api/batch/batch
ЁЄЁЄЁЄЁЄЁЄетвЛВПЗжЪ§ОнЪЁТдСЫ
ЁЄЁЄЁЄЁЄЁЄетвЛВПЗжЪ§ОнЪЁТдСЫ
0810: 4E 4B 4E 4F 57 4E 25 32 32 25 32 43 25 32 32 61 NKNOWN%22%2C%22a
0820: 62 69 25 32 32 25 33 41 31 25 37 44 26 63 75 72 bi%22%3A1%7D&cur
0830: 69 64 65 6E 74 69 74 79 3D 30 26 72 65 71 5F 74 identity=0&req_t
0840: 69 6D 65 3D 31 37 37 31 37 34 31 30 38 34 33 30 ime=177174108430
0850: 32 26 75 6E 69 71 69 64 3D 33 38 38 30 35 32 35 2&uniqid=3880525
0860: 61 2D 62 64 62 39 2D 34 31 66 62 2D 62 38 62 63 a-bdb9-41fb-b8bc
0870: 2D 62 33 38 64 31 61 64 64 64 32 32 39 26 76 3D -b38d1addd229&v=
0880: 31 33 2E 31 34 31 61 33 30 38 66 33 36 32 38 62 13.141a308f3628b
0890: 33 66 33 39 66 37 64 33 35 63 64 65 62 65 62 36 3f39f7d35cdebeb6
08A0: 39 32 30 65 32 31 920e21
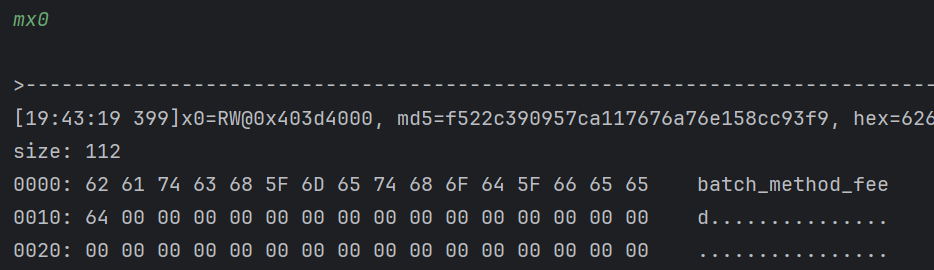
- ЗЕЛижЕашвЊЯТвЛИіblrЖЯЕуШЅПДЕБЪБЕФx0ЃЛ
- ЪЧНсЙћЮовЩЃЌВЂЧвВЮЪ§ЪЧЮвУЧДЋЕнЕФЖЋЮїЃЌЕЋЪЧНсЮВИНМгСЫвЛЕуЖЋЮїЃЌa308f3628b3f39f7d35cdebeb6920e21ЃЛ
- ПДЦ№РДЪЧвЛИібЮЃЌЯШВЛЬжТлЫћЪЧЗёЙЬЖЈЃЌЯШЗжЮівЛЯТЫуЗЈЃЌ32ЮЛЕФНсЙћЮвКмФбВЛЭљФЧЗНУцЯыЃЛШЅВтЪдвЛЯТЃЛ
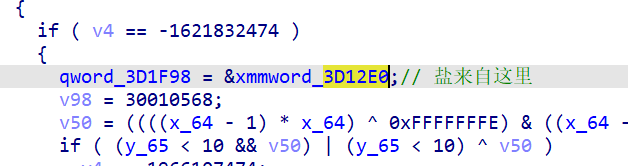
- ЮвУЧВТЕФВЛДэЃЌsigЪЧвЛИіМгбЮЕФmd5ЫуЗЈЃЌЭљЩюДІЩдЮЂИњвЛЯТвВПЩвдПДЕНЙиМќЕФmd5_transformКЏЪ§ЃЛ
- ЮвЗжЮіСЫвЛЯТЃЌгІИУЪЧЙЬЖЈаДЫРЕФЃЌОпЬхЕФЮЛжУЪЧетПщЃЛ
-
дкФкДцРяdumpШЗЪЕЪЧ a308f3628b3f39f7d35cdebeb6920e21 етИіжЕЃЌНЛВцв§гУЗЂЯжећИіКЏЪ§ЪЧдкjni_onloadБЛЕїгУЕФЃЌДѓИХТЪЪЧollvmЕФзжЗћДЎНтУмКЏЪ§ЃЌетРяЮвЯШВЛЙмСЫЃЌгааЫШЄЕФПЩвдИњвЛЯТЃЛ
-
Ыљвдsig= V3.0+md5(urlpath+ЧыЧѓВЮЪ§)ЃЌЧыЧѓВЮЪ§гаurlБрТыЃЌКУЯёЛЙЪЧСНВуЃЌИДЯжЕФЪБКђашвЊзЂвтЃЛ
4.2 sp
- НгЯТРДЗжЮіspЃЌдкЗжЮіЮвУЧзюКУЪЧзівЛЕуМђЕЅЕФВ№НтЃЌетУДГЄЕФУмЮФЃЌДѓИХТЪВЛЛсЪЧЙўЯЃЃЌМЋгаПЩФмЪЧЖдГЦМгУмЃЌвЊУДЪЧЗжзщвЊУДЪЧСїМгУмЃЛЮоТлФФжжЃЌЮвУЧЖМВЛЯЃЭћЗжЮіЕФЪБКђгаЗЧГЃЖрЕФЗжзщЃЌЫљвдЮвдкПЊЪМЗжЮіЧАНЋУїЮФИФГЩЖЬвЛЕуЕФаЮЪНЃЌИФГЩЪВУДЮоЫљЮНЃЌОЭгУЮвЧАУцЕФ call ОЭКУЃЌЖЬвЛЕуБШНЯКУЗжЮіЃЌЖјЧвЮвУЧбщжЄЙ§СЫunidbgХмГіРДНсЙћЪЧУЛЮЪЬтЕФЃЛ
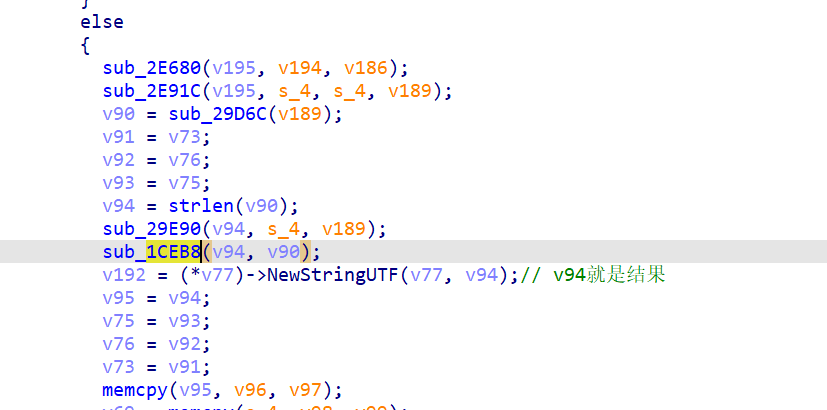
- жДааНсЙћЃК
JNIEnv->NewStringUTF("zwp_NCTRJTSwi3DepMLkHOGFvU0aAIbycf2I7pY7DTCAI7RtvzRtOHFggw~~") was called from RX@0x40021020[libyzwg.so]0x21020
[+]call_sp result:zwp_NCTRJTSwi3DepMLkHOGFvU0aAIbycf2I7pY7DTCAI7RtvzRtOHFggw~~
- КЭЧАУцЪЧЪЧвЛИівтЫМЃЌздМКИФвЛЯТjnienvРраЭЃЛ
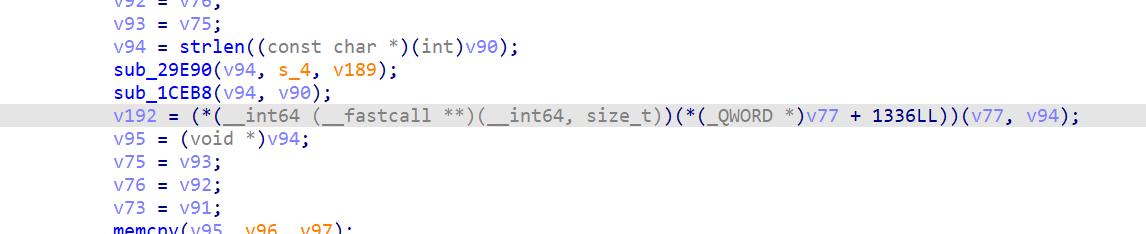
- ЯШhook 1CEB8ПДПДЃЛЫќгаСНИіВЮЪ§ЃЌЕкЖўИіЪЧвЛИіГЄЖШЃЛ
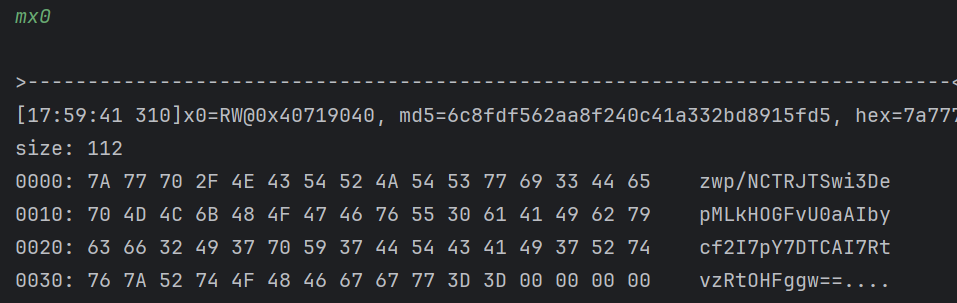
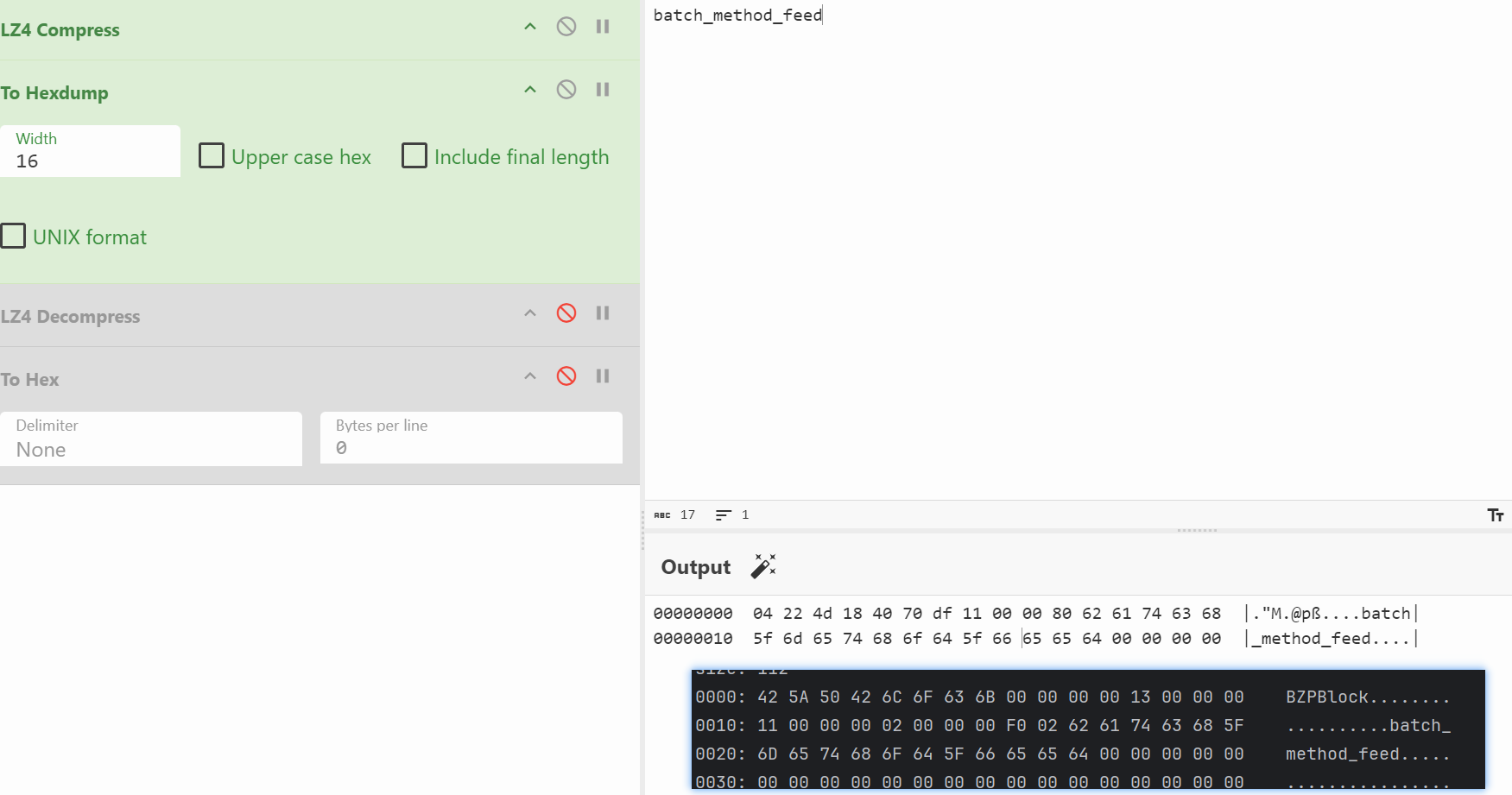
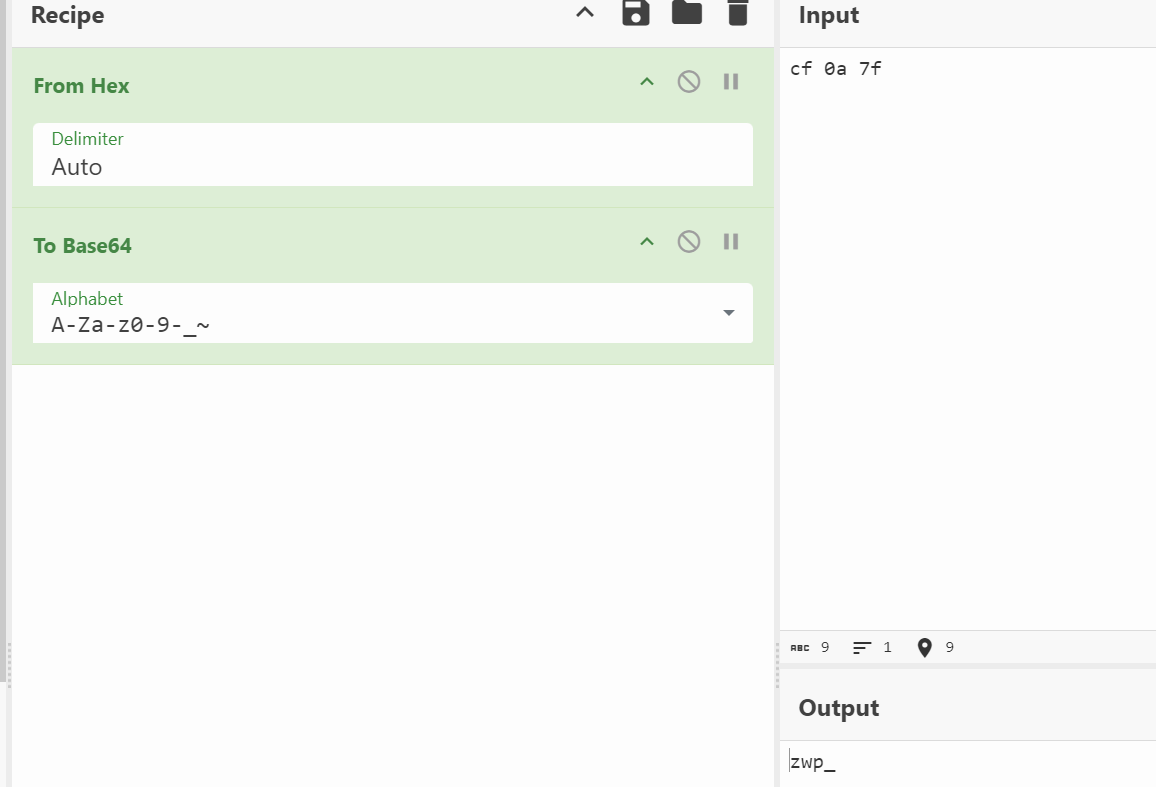
- етЪЧвЛИіbase64ЕФЪ§ОнЃЌПДПДЗЕЛижЕЪЧЪВУДЃЛ
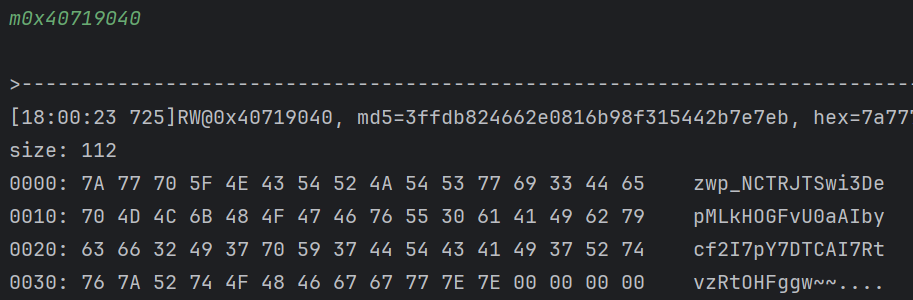
- ЗЕЛижЕОЭЪЧзюжеЕФНсЙћЃЌФЧУДетИіКЏЪ§жЛЪЧАбbase64Ъ§ОнзіСЫвЛЕуДІРэЃЛ
/ -> _
+ ->-
= -> ~
- ФЧЫќЧАУцЕФsub_29E90КЏЪ§ДѓИХТЪОЭЪЧbase64КЏЪ§СЫЃЛМЬајhookПДПДЃЌЫќгаШ§ИіВЮЪ§ЃЌВЮЪ§1ЪЧЛКГхЧјЃЌВЮЪ§3ЪЧГЄЖШЃЌгІИУЪЧВЮЪ§2ЕФГЄЖШЃЛ
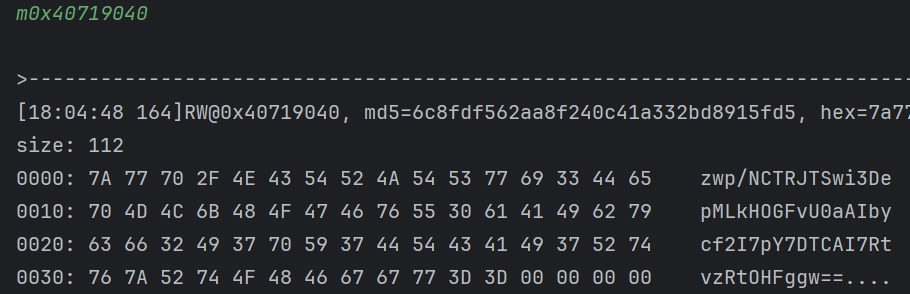
- ШЗЪЕЪЧbase64ЕФНсЙћЃЌЮвУЧШЅПДПДЪЧВЛЪЧБъзМЕФbase64ЃЛ

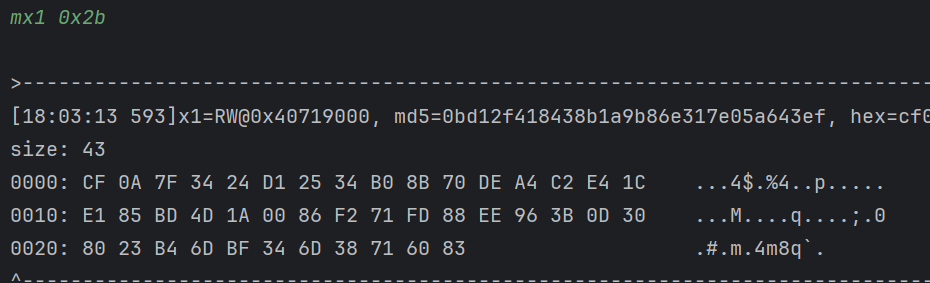
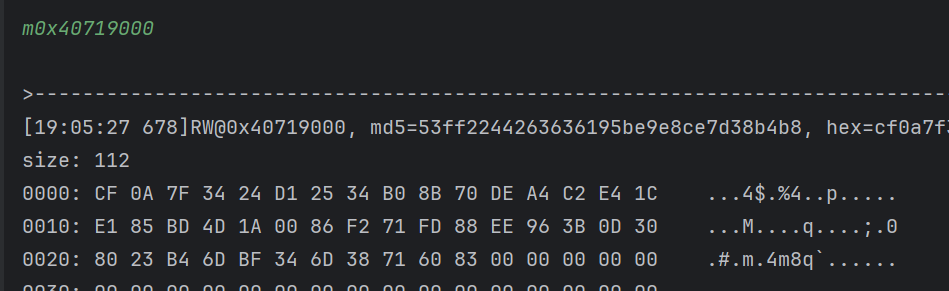
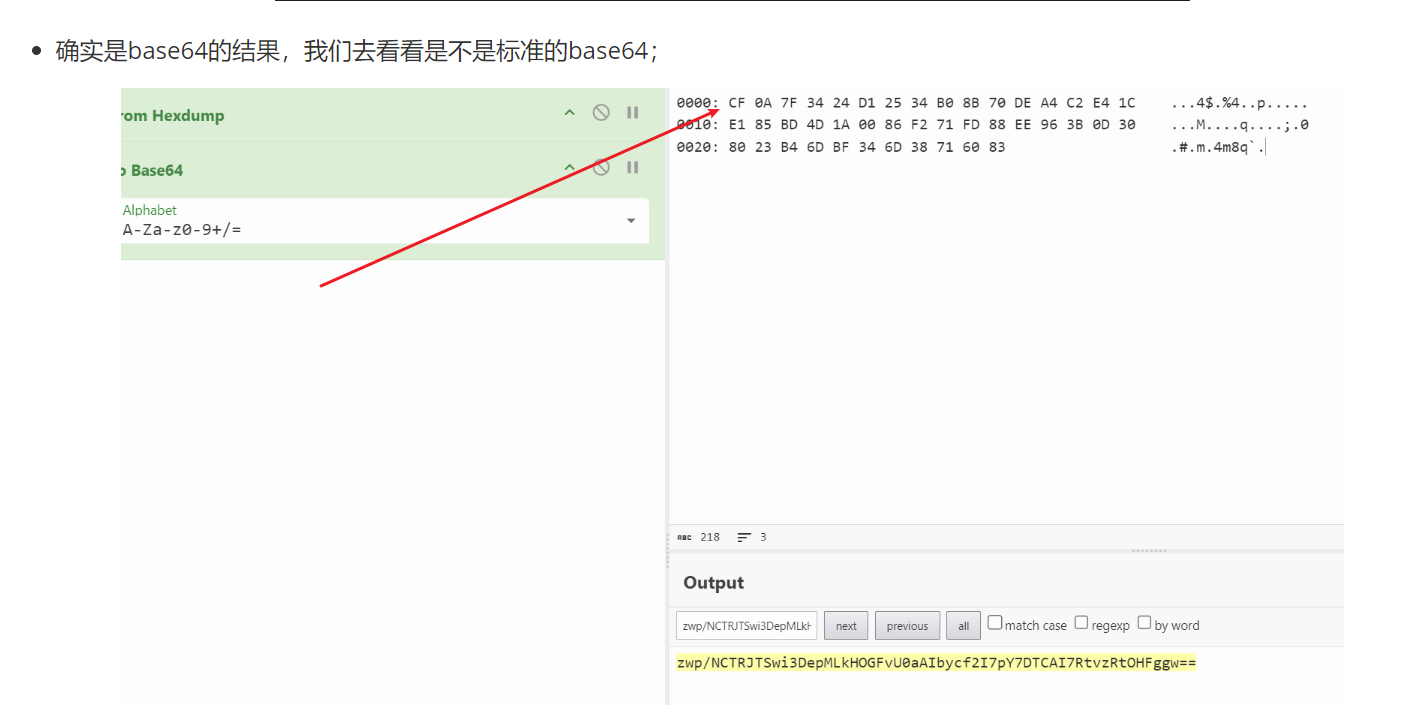
- ЪЧБъзМbase64ЮовЩЃЌЫљвдНгЯТРДЕФЮЪЬтОЭдкгкетЖЮУїЮФЪЧЪВУДЃП
0000: CF 0A 7F 34 24 D1 25 34 B0 8B 70 DE A4 C2 E4 1C ...4$.%4..p.....
0010: E1 85 BD 4D 1A 00 86 F2 71 FD 88 EE 96 3B 0D 30 ...M....q....;.0
0020: 80 23 B4 6D BF 34 6D 38 71 60 83 .#.m.4m8q`.
- ЭљЩЯПДОЭПЩвдПДЕНsub_2E91CгаЯрЙиЕФФкШнЃЛ
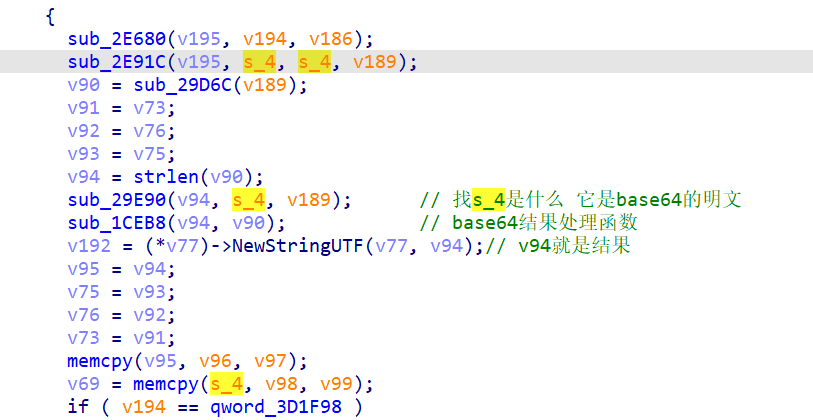
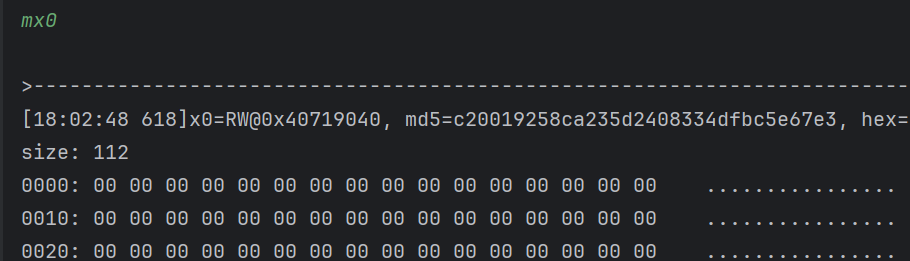
- hookПДПДЧщПіЃЌЫћвЛЙВгаЫФИіВЮЪ§ЃЌВЮЪ§ЖўКЭШ§ЪЧвЛбљЕФЃЛВЮЪ§ЫФЪЧ0x2bЃЛ
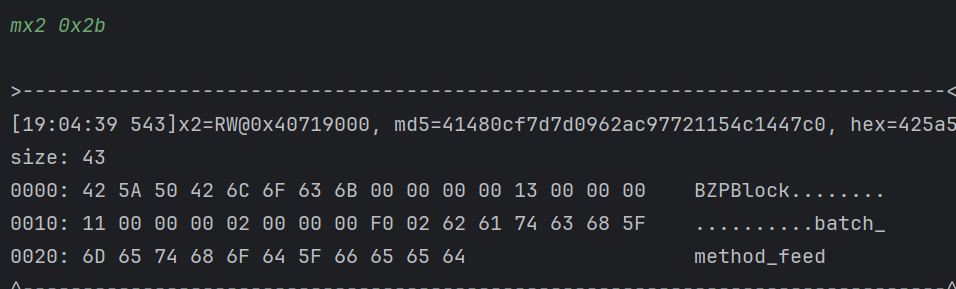
- ПДЦ№РДЖМВЛЪЧЬиБ№блЪьЃЌдйПДПДНсЙћАЩЃЛ
- НсЙћШЗЪЕЪЧЮвУЧашвЊевЕФbase64ЕФУїЮФФЧвЛВПЗжЃЌУЛгаЪВУДПЩПДЕФСЫЃЌНјетИіКЏЪ§ПДПДАЩЃЛ
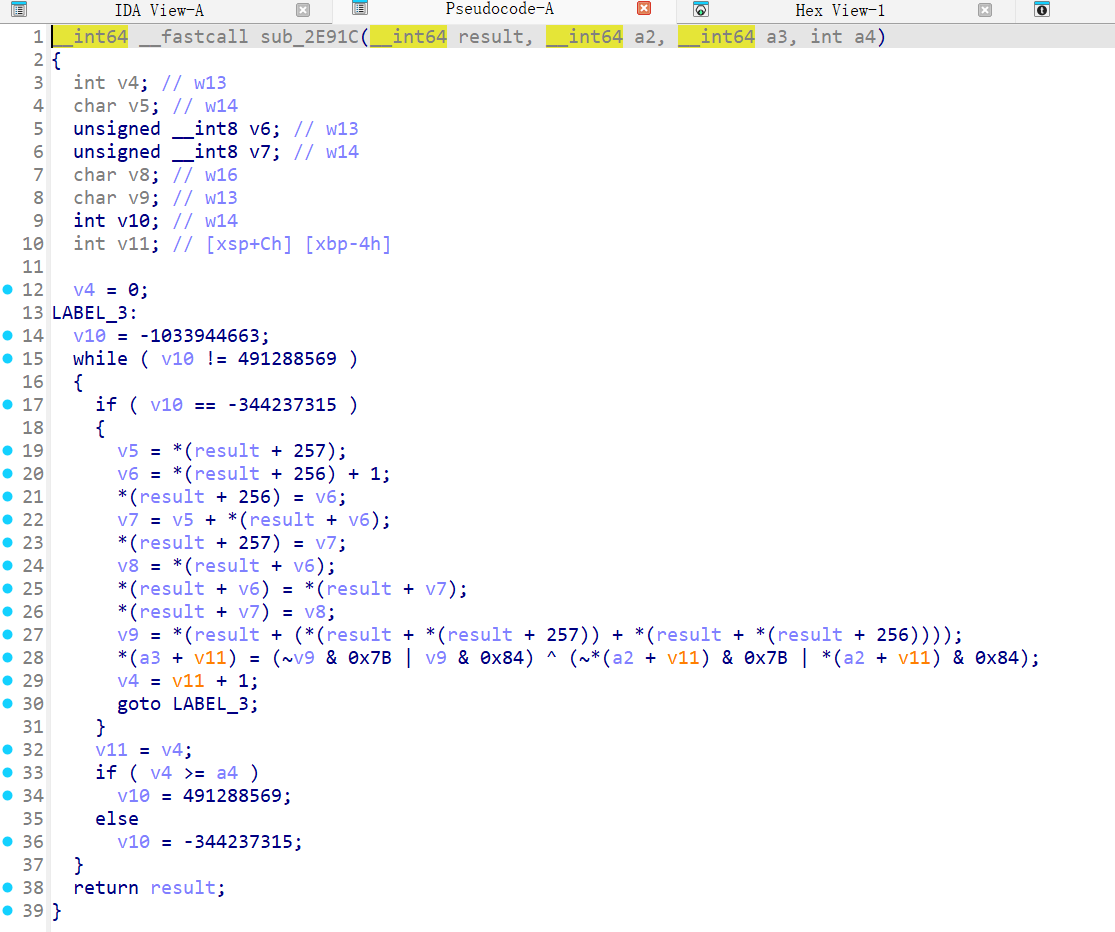
- змЬхВЛГЄЃЌЩдЮЂЪьЯЄвЛЕуЕФХѓгбгІИУФмПДГіРДЪЧЪВУДЫуЗЈЃЛ
*(data2 + v11) = (~v9 & 0x7B | v9 & 0x84) ^ (~*(data + v11) & 0x7B | *(data + v11) & 0x84)
- етвЛааЪЧгУзїЛьЯ§ЕФЃЌЛЏМђвЛЯТЪЕМЪЩЯОЭЕШгкЃК
*(data2 + v11) = v9 ^ *(data + v11)
- ВЛНіЪЧвьЛђЃЌЛЙга256ЃЌбЛЗЭЫГіЬѕМўвВЪЧУїЮФГЄЖШЃЌЫћгІИУЪЧвЛИіrc4ЫуЗЈЃЛ
void rc4_enc(unsigned char *S_Box, char *data, int data_len) {
int i = 0, j = 0, t = 0;
for (int k = 0; k < data_len; k++) {
i = (i + 1) % 256;
j = (j + S_Box[i]) % 256;
swap(S_Box[i], S_Box[j]);
t = (S_Box[i] + S_Box[j]) % 256;
data[k] = data[k] ^ S_Box[t];
}
}
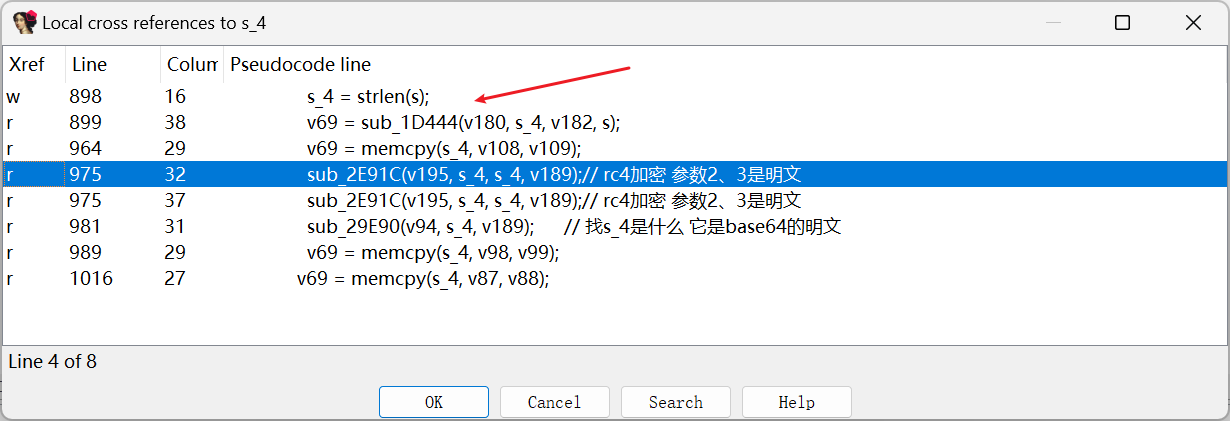
- ЦфЪЕЪЧБШНЯЯрЫЦЕФСЫЃЌВЮЪ§1гІИУОЭЪЧSКаЃЌВЮЪ§2ЁЂ3ОЭгІИУЪЧУїЮФЃЛ
- ЛЙгІИУгавЛИіДђТвsКаЕФКЏЪ§ЃЌЯыБиОЭЪЧЩЯУцетИіsub_2E680КЏЪ§СЫЃЛ
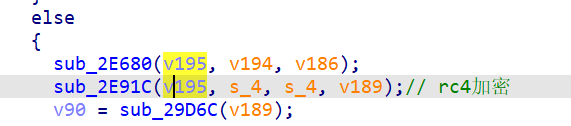
- hookПДПДЃЌгаШ§ИіВЮЪ§ЃЌВЮЪ§1ВЛжЊЕРЃЌВЮЪ§2гІИУЪЧkeyЁЂВЮЪ§3ЪЧkeyЕФГЄЖШЃЛ
- ЪЧЗёгааЉблЪьЃЌетИіkeyЪЧЧАУцsigЕФбЮЃЛФЧЮвУЧВтЪдвЛЯТНсЙћЪЧЗёЪЧЮвУЧЫљЯыЕФФЧбљЃЛ
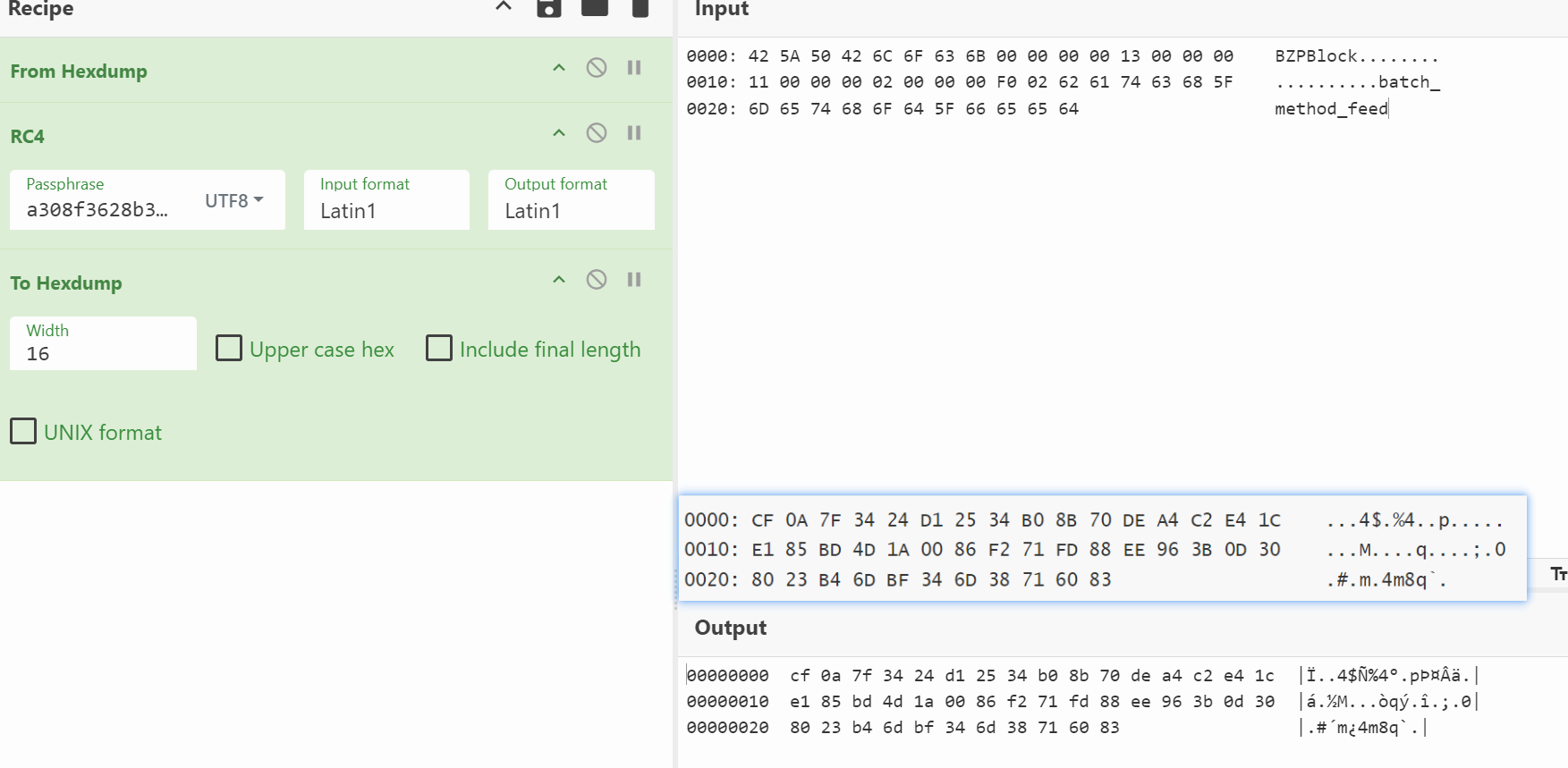
- ШЗЪЕЪЧБъзМЕФrc4ЫуЗЈЃЌЫљвдbase64ЕФУїЮФОЭРДздгкrc4ЫуЗЈЕФМгУмНсЙћЃЛетИіkeyЯыБивВЪЧЖдееЕФЃЌФЧУДЃЌrc4ЕФУїЮФгжЪЧЪВУДЃП
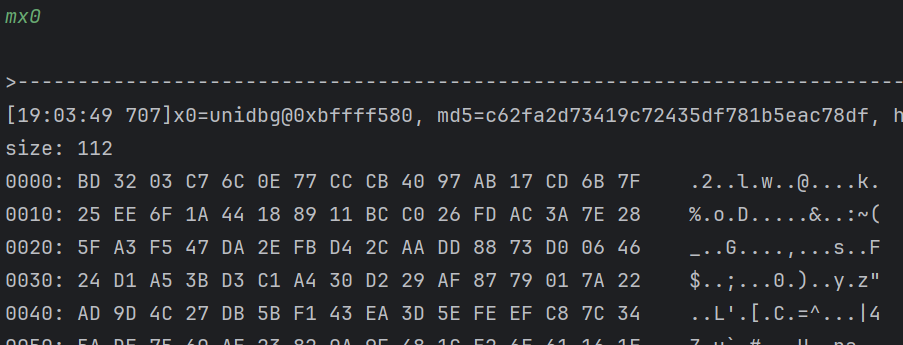
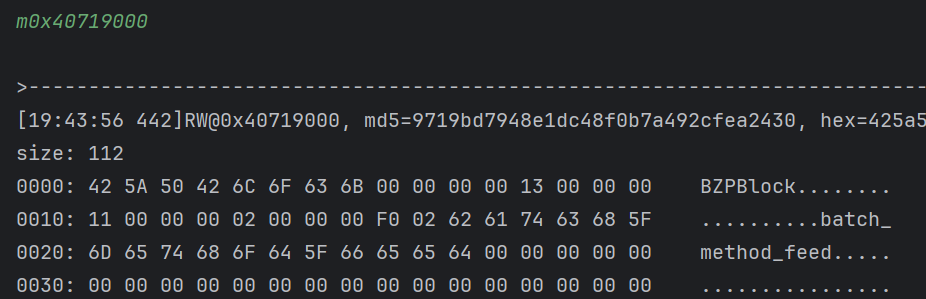
- ЫфШЛПДЦ№РДКЭЮвУЧЕФУїЮФВюВЛЖрЃЌЕЋЪЧЛЙЪЧгаЧјБ№ЕФЃЛ
0000: 42 5A 50 42 6C 6F 63 6B 00 00 00 00 13 00 00 00 BZPBlock........
0010: 11 00 00 00 02 00 00 00 F0 02 62 61 74 63 68 5F ..........batch_
0020: 6D 65 74 68 6F 64 5F 66 65 65 64 method_feed
- УїЮФЪЧЃКbatch_method_feedЃЌПДЦ№РДВюВЛЖрЃЛеввЛЯТетвЛВПЗждѕУДРДЕФЃЌШЅПДПДНЛВцв§гУЃЛ
- ЧАУцСНИіПДЦ№РДБШНЯгаПЩФмвЛЕуЃЌНјШЅПДПДЃЛ
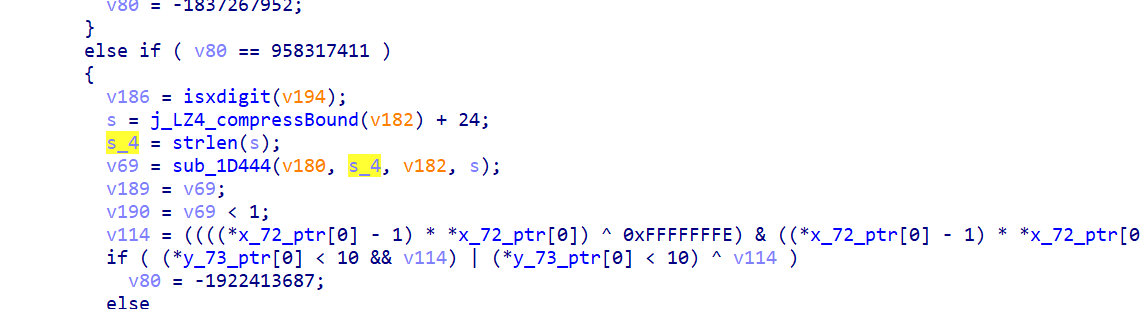
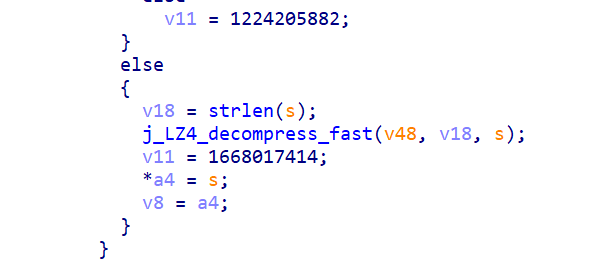
- гаИіj_LZ4_compressBoundКЏЪ§ЃЌетЪЧLZ4бЙЫѕЕФБъжОЃЌЫбЫївЛЯТетИіКЏЪ§ЪЧЪВУДЃЛ
int LZ4_compressBound(int inputSize);
- зїгУЃКМЦЫуИјЖЈЪфШызжНкЪ§
inputSize О LZ4 бЙЫѕКѓПЩФмВњЩњЕФзюДѓЪфГіГпДчЃЛ
- hookвЛЯТsub_1D444КЏЪ§ПДПДЃЌБЯОЙгаФПБъЃЛЫћвЛЙВгаЫФИіВЮЪ§ЃЛКѓУцСНИіЖМЪЧГЄЖШЃЌВЮЪ§3гІИУЪЧУїЮФЕФГЄЖШЃЛ
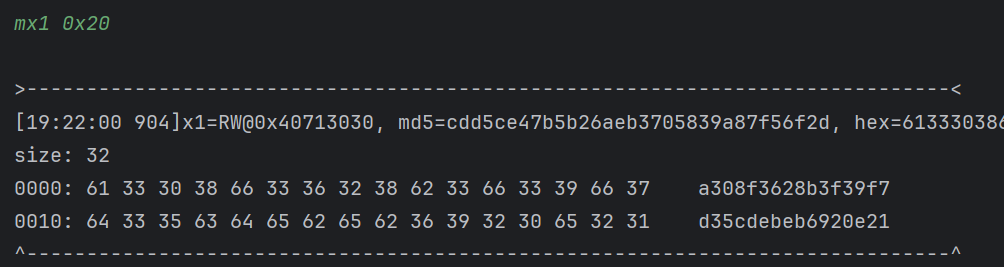
- x1ЪЧЛКГхЧјЃЌдЫааНсЪјКѓШЗЪЕЪЧЮвУЧвЊевЕФФЧвЛВПЗжЪ§ОнЃЌНјШЅКЏЪ§ФкВППДПДЃЛ
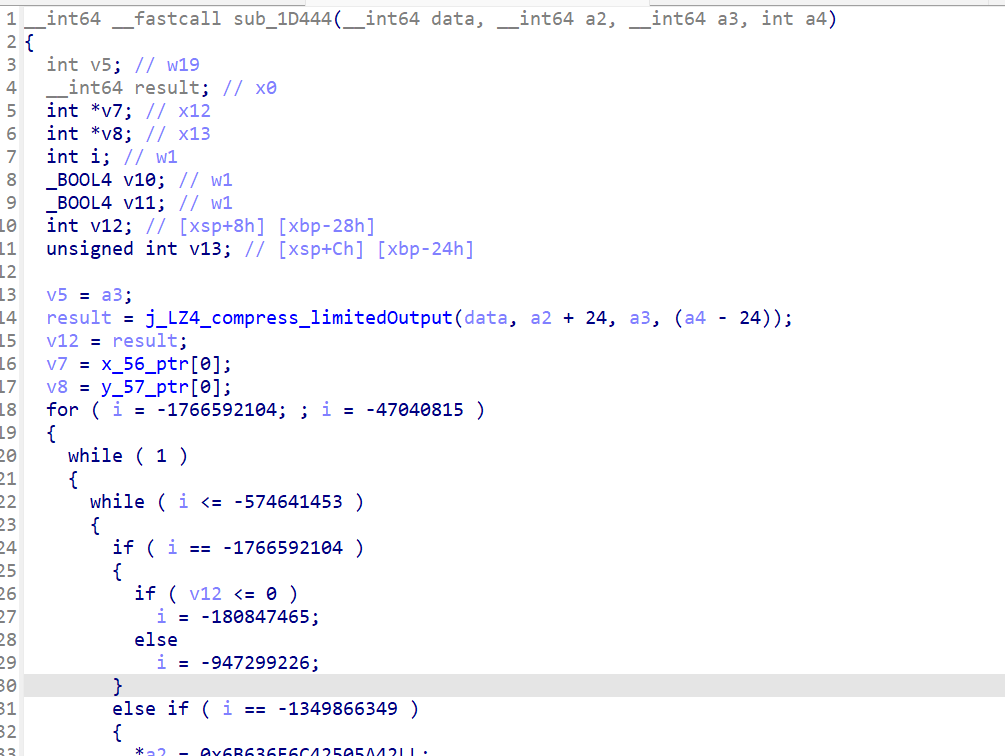
- вЛНјРДОЭПЩвдПДЕНвЛИіLZ4ЕФКЏЪ§ЃЌНсКЯЧАУцЕФЗћКХЮвУЧВТВтПЩФмЪЧвЛИіLZ4бЙЫѕЃЌЮвУЧГЂЪдШЅбЙЫѕвЛЯТПДПДЪЧЗёЪЧБъзМЕФЃЛ
- ПДЦ№РДВЂВЛвЛжТЃЌЪьЯЄбЙЫѕЫуЗЈЕФХѓгбгІИУжЊЕРЃЌбЙЫѕЫуЗЈЖМгавЛИіФЇЪ§ЃЌгУгкЗжБцЪЧФФвЛИібЙЫѕЫуЗЈЃЛ
- LZ4ЪЧ4зжНкЃЌаЁЖЫЃЌжЕЮЊ0x184D2204ЃЌПЩвдКЭБъзМЕФЖдБШПДПДЃЌШЗЪЕЪЧетбљЃЛЕЋЪЧЮвУЧЕФНсЙћКмУїЯдВЛвЛбљЃЌетРяЮвУЧШУaiУшЪівЛЯТLZ4бЙЫѕКѓЕФзщГЩЃЛ
- НсЙћЪєгкЪЧЭъШЋВЛЖдСЫЃЌгІИУЪЧФЇИФСЫетВПЗжЃЌПДПДДњТыВПЗжАЩЃЌЮваДСЫвЛЕуЕузЂЪЭЃЛ
-
бЙЫѕГЩЙІКѓЕФНсЙћВЂУЛгаЗХдкa2ЕФЮЛжУЃЌЖјЪЧЭљКѓХВСЫ24ИізжНкЃЌШЛКѓздЖЈвхСЫ24 зжНкЭЗВПЃЛ
-
НтЮівЛЯТетВПЗжздЖЈвхЃЌЦфЪЕОЭдкЯТЗНИпССДІЃЛЯШЪЧ8 зжНкФЇЪ§ЃЈЗЧБъзМЃЉЃЌвВОЭЪЧЙЬЖЈЕФ0x6B636F6C42505A42ЃЌетРяЪЧаЁЖЫађЕФЃЌШЛКѓЪЧ4 зжНкБЃСєзжЖЮЃЈжУ 0ЃЉЃЌбЙЫѕКѓГЄЖШЃЈ4 зжНкЃЉЃЌШЛКѓЪЧдЪМЪ§ОнГЄЖШЃЈ4 зжНкЃЉЃЌдйОЭЪЧдЪМГЄЖШ ^ бЙЫѕГЄЖШЃЈ4 зжНкаЃбщЃЉЃЛ
-
ЛузмвЛЯТЃК
- ЦЋвЦ 0ЃК8 зжНкФЇЪ§ 42 5a 50 42 6c 6f 63 6bЃЈЙЬЖЈЃЉЃЛ
- ЦЋвЦ 8ЃК4 зжНкБЃСєзжЖЮЃЈжУ 0ЃЉЃЛ
- ЦЋвЦ 12ЃКбЙЫѕКѓГЄЖШv12ЃЈ4 зжНкЃЉЃЛ
- ЦЋвЦ 16ЃКдЪМЪ§ОнГЄЖШv5ЃЈ4 зжНкЃЉЃЛ
- ЦЋвЦ 20ЃК
дЪМГЄЖШ ^ бЙЫѕГЄЖШЃЈ4 зжНкЃЉЃЛ
-
ЪЕМЪЩЯетИібЙЫѕжЛЪЧИФСЫЭЗВПФЧвЛВПЗжЃЌЦфЫћЕФЛЙЪЧБъзМЕФЃЌЫљвдЮвУЧШчЙћашвЊНтбЙЫѕЕФЛАашвЊШЅЕєЖдгІЕФ24зжНкЃЌШЛКѓдйНтбЙЫѕЃЛетвЛВПЗжЮвВШПгСЫЃЌДЋВЮГіЮЪЬтСЫЕМжТвЛжБГіДэЃЌИуЕУЮвЛЙвдЮЊВЛЪЧБъзМЕФбЙЫѕЃЛ
-
ЩдЮЂзмНсвЛЯТspЕФЫуЗЈЃК
- ЪзЯШЪЧLZ4бЙЫѕУїЮФЃЌЕЋЪЧетРяИФСЫвЛЕуЭЗВПЦДНгЃЌОЭдкЩЯУцгаОпЬхИФСЫЪВУДЃЛ
- lz4бЙЫѕКѓНјааRC4МгУмЃЌУидПЪЧsigФЧИібЮЃКa308f3628b3f39f7d35cdebeb6920e21ЃЛ
- зюКѓНјааbase64БрТыЃЌТыБэЩдЮЂгаЕуИФЖЏЃЌвВПЩвдБъзМБрТыКѓЬцЛЛФЧМИИіЗћКХЃЛ
-
етИіашвЊСЫНтLZ4бЙЫѕЕФЯИНкЃЌЮввВВЛЪЧЬиБ№ЪьЯЄЃЌЗХвЛИіНтУмspЕФdemoдкетЃЌПЩвдздааВтЪдЃЛ
import base64
import struct
import lz4.block
from Crypto.Cipher import ARC4
def base64_decode_custom(b64_str: str) -> bytes:
"""
здЖЈвхBase64НтТыЃЈТыБэ: A-Za-z0-9-_~ЃЉ
"""
BASE64_ALLOWED = "ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789-_~"
cleaned = ''.join(c for c in b64_str if c in BASE64_ALLOWED).replace('~', '=')
cleaned += '=' * ((4 - len(cleaned) % 4) % 4)
return base64.urlsafe_b64decode(cleaned.encode())
def rc4_decrypt(data_bytes: bytes, key_hex: str = "a308f3628b3f39f7d35cdebeb6920e21") -> bytes:
key_bytes = key_hex.encode()
return ARC4.new(key_bytes).decrypt(data_bytes)
def lz4_decompress_custom(packed_data: hex) -> bytes:
"""
ЛЙд sub_1D444ЃКНтЮіЭЗВП + LZ4НтбЙ
:param packed_data: ЗтзАКѓЕФбЙЫѕЪ§Он
:return: дЪМУїЮФ
"""
if len(packed_data) < 24:
raise ValueError("Ъ§ОнЬЋЖЬ")
magic, _, comp_len, orig_len, chk = struct.unpack('<QIIII', bytes.fromhex(packed_data)[:24])
if magic != 0x6B636F6C42505A42 or chk != (orig_len ^ comp_len):
raise ValueError("аЃбщЪЇАмЃКЗЧФПБъИёЪНЛђЪ§ОнЫ№ЛЕ")
compressed = bytes.fromhex(packed_data)[24:24 + comp_len]
return lz4.block.decompress(compressed, uncompressed_size=orig_len)
if __name__ == "__main__":
B64_STRING = "xxx"
decoded = base64_decode_custom(B64_STRING)
decrypted = rc4_decrypt(decoded)
result = lz4_decompress_custom(decrypted.hex())
print(result.decode())
- Ыљвдsp=base64( RC4 (ФЇИФLZ4бЙЫѕ (urlpath+ЧыЧѓВЮЪ§) ) )ЃЌзмЬхОЭЪЧетИібЙЫѕПЩФмЗбЕуЪБМфЃЌЪЃЯТЕФОЭЪЧЯьгІЕФНтУмСЫЃЛ
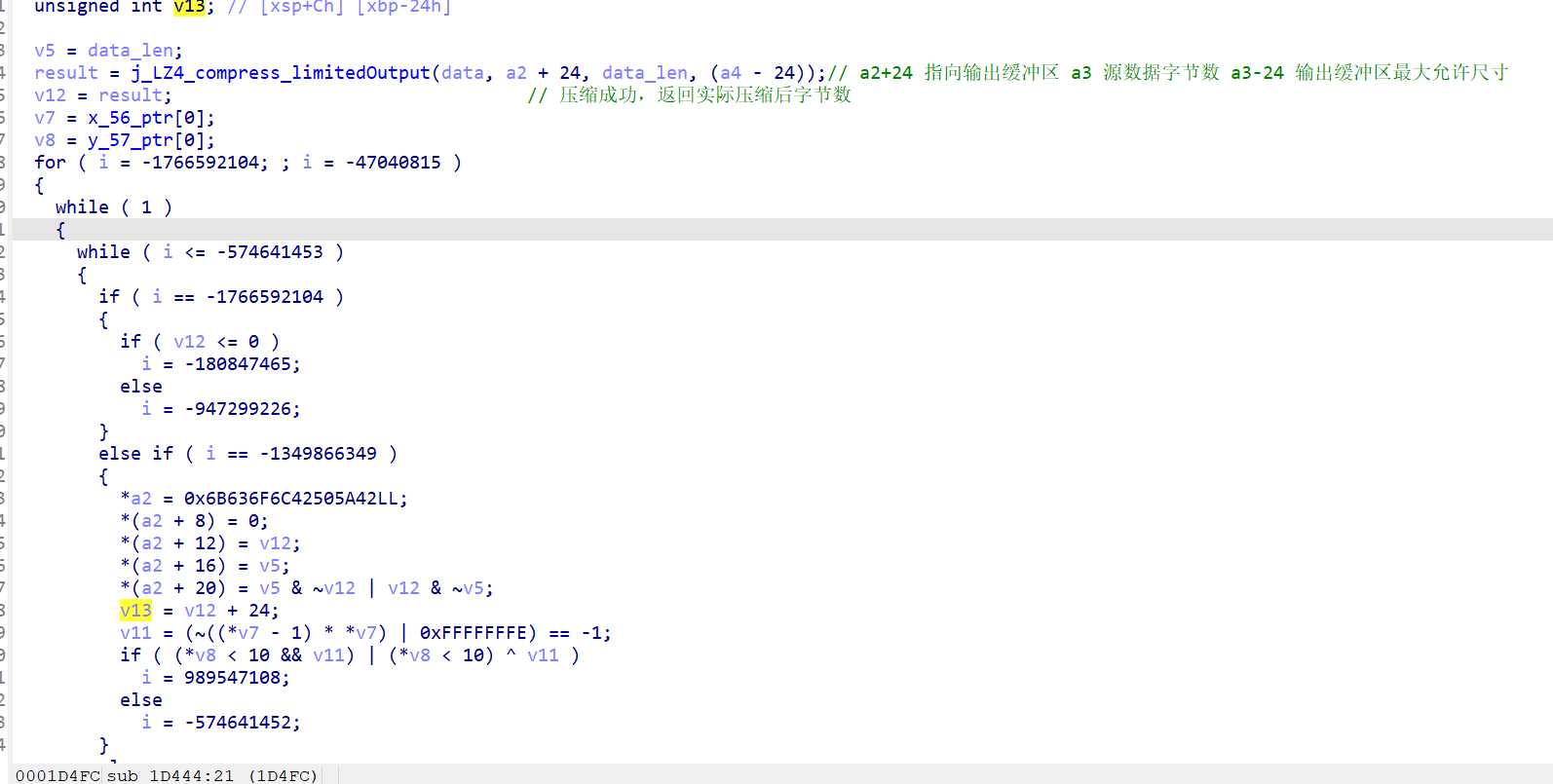
4.3 ЯьгІНтУм
- жБНгЕїгУКЏЪ§ЃЌПДПДгаУЛгаЪВУДаХЯЂАЩЃЛ
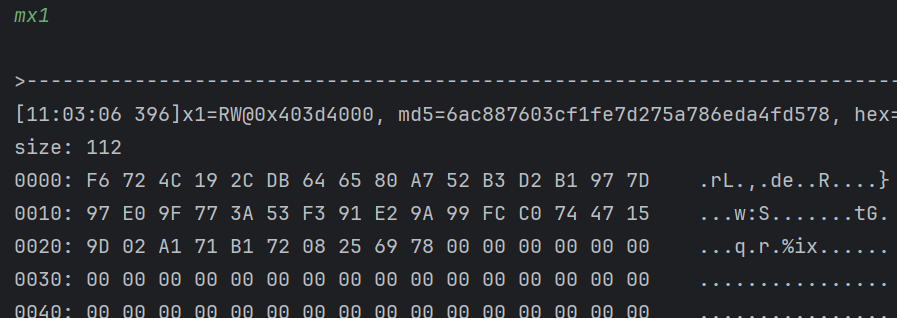
- аХЯЂВЛЖрЃЌЕЋЪЧЛЙЪЧгавЛЕуЃЌетИі0xf6724c192cЪЧЪВУДЃПИаОѕгІИУЪЧУмЮФЕФЪЎСљНјжЦЃЌзЊвЛЯТПДПДЃЛ
- ШЗЪЕЪЧетбљЃЌФЧШЅПДвЛЯТ0x25440етИіЕижЗЃЛ
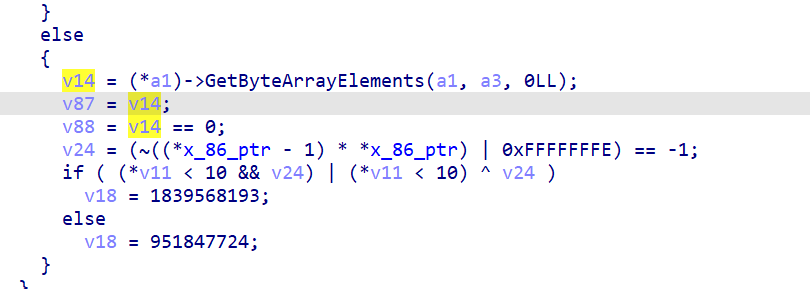
- НјРДЛЙЪЧздМКАбРраЭИФе§вЛЯТЃЌе§КУТфдкећИіНтУмКЏЪ§РяЃЌДѓИХгаМИАйааЃЌЮвУЧЩдЮЂПДПДАЩЃЛАбЪѓБъЗХдкВЮЪ§1ЩЯЃЌПДПДНЛВцв§гУЃЛ
- ЮвИіШЫОѕЕУЛёШЁГЄЖШКЭЫќБОЩэЪЧБШНЯУєИаЕФВйзїЃЌвВОЭЪЧЯТУцетШ§ИіЕиЗНЃЛ
- ПЩвдЖМШЅПДПДЃЌгаУЛгаЪВУДЙиМќЕФаХЯЂЃЛ
- ВЛЖЯЕиевНЛВцв§гУХфКЯБфСПУћЕФаоИФОЭКУЃЌевЕНетбљвЛИіЮЛжУгаКЏЪ§ЕїгУЃЛ
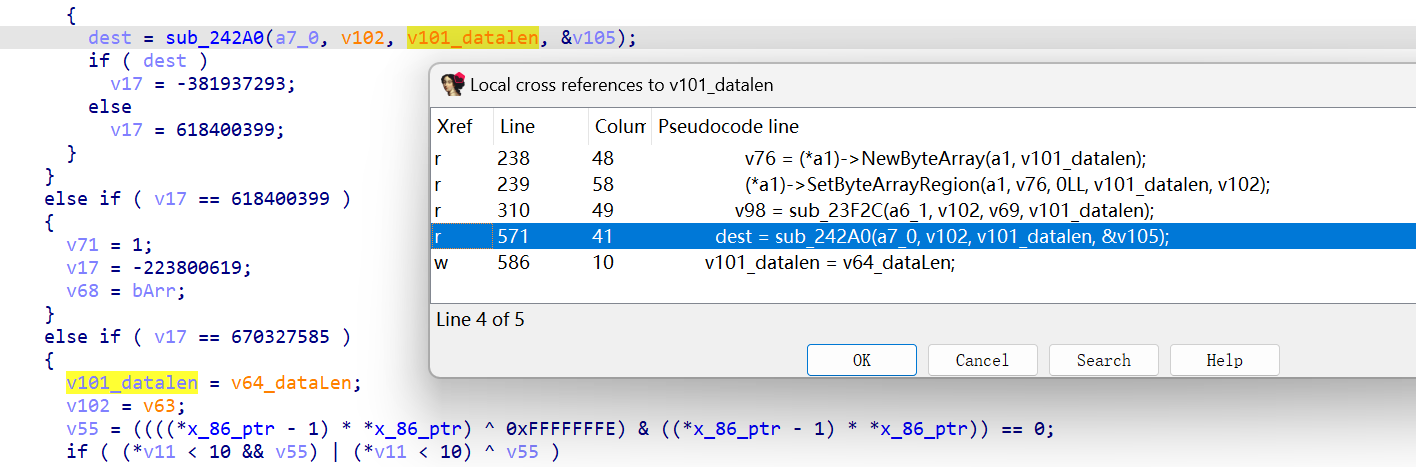
- ПДЦ№РДsub_23F2CКЭsub_242A0ПЩФмЛсЪЧФПБъЃЌНјsub_23F2CПДПДЃЛ
- МЧвфСІКУвЛЕуЕФХѓгбгІИУФмПДГіРДетЪЧФФРяЃЌЯШВЛБэЃЌhookПДПДЪЧВЛЪЧзпСЫЃЛЫћвЛЙВга4ИіВЮЪ§ЃЌВЮЪ§1ЪЧ1ЃЌВЮЪ§2ЁЂ3гІИУЪЧЕижЗЃЛ
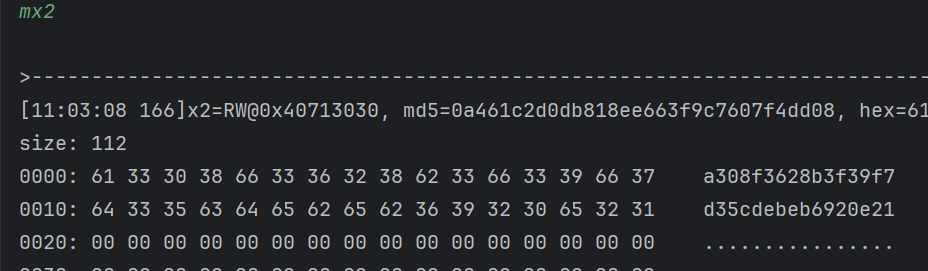
- ВЮЪ§2КмЯдШЛЪЧЮвУЧЕФУїЮФЃЌВЮЪ§3ЪЧrc4ЕФkeyЃЌФЧетИіКЏЪ§ЪЧВЛЪЧrc4ФиЃПД№АИЪЧЯдШЛЕФЃЛ
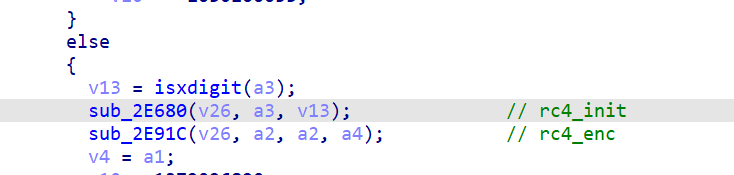
- ЫљвдЯьгІЕФЫуЗЈЪЕМЪЩЯКЭspЪЧЗДзХРДЕФЃЌspМгУмЯьгІНтУмЃЌЕЋЪЧЯьгІЪЧУЛгаbase64ЕФЙ§ГЬЕФЃЛЦфЪЕдкЗжЮіжЎЧАЮвОЭжЊЕРДѓИХЪЧвЛбљЕФЫуЗЈСЫЃЌЮвУЧзЅАќЕФЯьгІНсЙћЕФПЊЭЗЪЧЃК
- АбЫќЧАУцМИИізжНкbase64вЛЯТЃЛ
- ЖјЧвдкЗжЮіspЕФЪБКђЖрДЮгаетжжПЊЭЗЕФhexЪ§ОнЃЌШчЯТЭМЃК
- етЖМЪЧПЩвдВТВтЕФЃЌетРяОЭСФетУДЖрЃЌЫуЗЈЛЙУЛгаЭъШЋНсЪјЃЛ
- етИіЪ§ОнжЛЪЧОЙ§СЫrc4НтУмЃЌЕЋЪЧУЛгаlz4НтбЙЫѕЕФФкШнЃЌБ№ЭќСЫЮвУЧЕФНсЙћЦфЪЕКмГЄЕФЃЛПЩвдАбВЮЪ§ЛЛГЩГЄЕФдйЕїгУвЛЯТЃЛ
- ideaЯдЪОЗНЗЈЬЋГЄСЫЃЌЮветЛсгжУЛаДМгУмКЏЪ§ЃЌжБНгШЅПДСэвЛИіЗНЗЈАЩЃЛ
- ЪЕМЪЩЯОЭЪЧдкНтУмЧАНтвЛДЮбЙЫѕЃЌЦфгрУЛЩЖЧјБ№ЃЌетРявВУЛгаbase64ЃЛ
- ОЭгУЧАУцФЧИіspНтУмЕФНХБОвВПЩвдНтПЊГЄЕФУмЮФЃЛ
- ЕНетРяШ§ИіЮЛжУЕФЫуЗЈЖМНВЧхГўСЫЃЌЯьгІНтУмКЭspЪЧРрЫЦЕФФцЙ§ГЬЃЛ
5. змНс
- Г§СЫетвЛжжУмЮФвдЭтЃЌЮвЛЙЗЂЯжСЫгаЖржжУмЮФЃЌЮввдspКЭЯьгІЖдеезХЫЕвЛЯТЃК
БОЮФНВЕФЃК
spЃКzwp_NПЊЭЗ
ЯьгІЃКcf 0a 7f 34ПЊЭЗ ЯьгІЛЙгавЛжжЖЬЕФ ПЊЭЗВЛМЧЕУСЫ
spЃКwxJRBAfMjnnПЊЭЗ
ЯьгІЃКc3 12 51 04ПЊЭЗ
spЃКwxJRBAfMjnnПЊЭЗ
ЯьгІЃКfa 6a 62 29ПЊЭЗ етИіЪєгкЖЬЕФ КЭЧАУцЕФРэТлвЛбљ УЛгабЙЫѕ жЛгаrc4НтУм
- ДѓИХОЭЪЧЫФжжЃЌгаПЩФмИќЖрЃЌБЯОЙЮввВжЛЪЧЫцБуПДСЫМИИіНгПкЃЛКѓУцетжжЦфЪЕЫуЗЈЪВУДЖМЪЧвЛбљЕФЃЌОЭЪЧrc4ЕФkeyВЛвЛбљЃЌвВВЛФмЫЕВЛвЛбљЃЌЖрСЫЕуЖЋЮїЖјвбЃЌИааЫШЄЕФздМКПДПДОЭКУЃЛ
- змНсвЛЯТетМИИіВЮЪ§ЃК
- sigЃКmd5МгбЮЃЌбЮЪЧrc4ЕФkeyЃЛ
- spЃКbase64 + rc4 + lz4бЙЫѕЃЛ
- ЯьгІЃКЭЌspЃЛ
- byЃК2026-02-23ЃЛ